-
Locate the Utimaco JCE configuration file in your SecurityServer directory,
Linux/x86-64/Crypto_APIs/JCE/sample/CryptoServer.cfg. -
Create a non-root user and set its password.
|
›_ Console |
|
|
-
Copy the Utimaco JCE configuration file
CryptoServer.cfgto the user's home directory.
|
›_ Console |
|
|
-
Create one Cryptographic User with CXI group.
|
›_ Console |
|
|
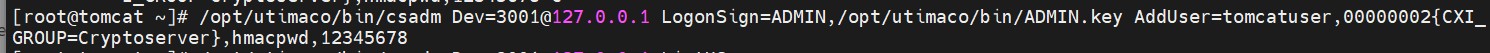
User creation with csadm
-
Edit the
$home/CryptoServer.cfgfile and make the appropriate changes to the file.
|
CryptoServer.cfg |
|---|
|
|
For more information regarding the commands and command parameters please check
the CryptoServer documentation. The device may be a CryptoServer (PCIe or LAN) device.
The device line will follow one of these patterns, based on the HSM form-factor:
Device = 288@<HSM IP address> Hardware (LAN) HSM
OR
Device = /dev/cs2.0 Hardware (PC Ie) HSM
To make your testing easier, it would be good to enable the Cryptoserver JCE log file. That can be enabled by editing the Logging Loglevel. Set the LogFile and Logging Loglevel to 1. For testing you may want to increase it to 4. The added LogFile points to a file. If you encounter problems, check the log file named CryptoServerJCE.log in the LogFile defined file. When you are done testing, you should change Logging to 1 or 2. This limits the logging to only critical and important messages.
-
Obtain the below jurisdiction (unlimited strength) policy files from Oracle for your country and Java version:
US_export_policy.jar
local_policy.jar
The unlimited policy files are required only for JDK 8 updates earlier than 8u161. On those versions and later, the stronger cryptographic algorithms are available by default.
-
Copy these jurisdiction policy files into the directory <java-home>/lib/security.
|
›_ Console |
|
|