The SecurityServer EKM provider exposes basic authentication to the SQL Server using username/-password pairs. These pairs are stored in so-called credentials that need to be created per EKM provider. Finally, a credential is mapped to an SQL Server login.
If a logged-in user wants to access a certain EKM provider, the credential mapped to both the login and the EKM provider is looked up, and the username/password is passed to the EKM provider. The SecurityServer EKM provider uses this information to perform a login on the SecurityServer.
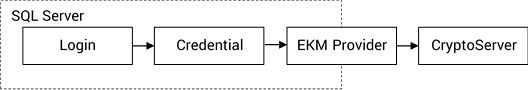
Credential Mapping
Multiple SQL Server logins can use the same credentials. If the EKM providers are different, a login can be used with multiple credentials. Otherwise, the lookup shown before will fail.
The following SQL will create a credential csekm for the SecurityServer user sqlekm with the password utimaco.
CREATE CREDENTIAL csekm WITH IDENTITY = 'sqlekm', SECRET = 'utimaco'
FOR CRYPTOGRAPHIC PROVIDER utimaco
GO
Creating a cHSM user needs to be done either via csadm or CAT.
For detailed information, refer to chapter 3.3 of the u.trust Anchor cHSM Administration Manual.
Use the following SQL statement to map the credential to any SQL Server account. You can, for example, substitute <user> with an integrated account like sa or a Windows account like [DB1\Administrator].
ALTER LOGIN <user> ADD CREDENTIAL csekm
GO