The following Figure shows an overview of the process of creating a remote signature using the SAM.
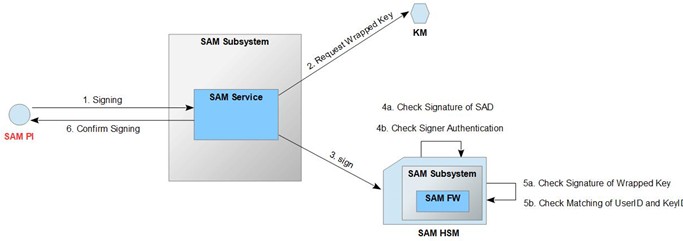
Figure 21: Overview of the Signing operation flow
A Signer uses the SAM peer interface to request the operation. Authentication and identification of the requesting Signer is required beforehand.
When the request is retrieved, the SAM service checks whether the requesting Signer is identified and authenticated.
If the check regarding identity and authenticity is successful, the SAM service requests the signing of the data to be signed, which is transferred with the received request. In detail, the SAM service requests
the wrapped key referenced in the SAD and
the signing of the data to be signed at the SAM HSM. The SAM firmware verifies that:
the authenticity of the Signer and the signature of the SAD are valid. the signature of the Wrapped Key is valid.
the user ID and the key ID of SAD of the Wrapped Key match.
If these steps are successful (validated), the data to be signed is signed at the SAM of the cryptographic module and returned to the SAM service. Otherwise, an ''error'' is returned.
The SAD basically has the following structure: {SignerAuthenticationData, KeyID, DTBS/R}. Reference] contains a more detailed ASN.1 definition of the structure.
|
Purpose |
This operation is invoked by the Signer to create a signature using a qualified signature key. |
||
|
Interface |
SAM Peer Interface (see [IF_SPI]) |
||
|
Method of use |
The operation is called by a client software according to the specification of the SAM peer interface (see [IF_SPI]). |
||
|
Input |
Parameter |
Type |
Description |
|
|
|||
|
|
sad |
Binary |
The Signed ASN.1 structure contains the following components: ID token of the user KeyID of the key to be used for remote signing Hash value(s) to be signed Algorithm for signature generation |
|
Output |
Parameter |
Type |
Description |
|
sigbin |
Binary |
Signature binary returned by the cryptographic module. |
|
|
Error messages |
Type |
Reason |
|
|
ContainerParseError |
If the input cannot be parsed into a message container |
||
|
MessageParseError |
If the input data cannot be parsed into the specified message type |
||
|
UnknownMessageType |
The contained message type was not known to the processor |
||
|
UnknownCredentialType |
The credential type included was not known to the processor |
||
|
AuthenticationError |
The credential could not be validated |
||
|
UnknownUser |
The credential could not be associated with a user |
||
|
NotAuthorized |
If the acting user is not authorized to perform the current operation If the acting user does not have access to the specified KeyID |
||
|
NotOperational |
A component (e.g. database, HSM) is not available or not in an operational state |
||
|
UnexpectedError |
When an error condition occurs that was not anticipated |
||
|
NotFound |
A key corresponding to the passed keyid does not exist. |
||
|
InvalidAlgorithm |
Specified signature algorithm does not match the key algorithm. Specified hash algorithm does not match digest size. |
||
|
InvalidAuthentication |
Identity token in SAD does not pass signature verification. UserID in the identity token does not match the UserID provided by the credential. Identification level is not sufficient (at least 'substantial'). |
||
|
InvalidSignature |
SAD signature cannot be verified with the public key embedded in the identity token. |
||
|
Security Audit Log Entry |
In case of success An audit record is created that contains at least the following information |
|
|
|
|
|
In case of an error |
|
|
The following errors emit regular log messages, but no audit log entries (since no acting user could be derived): |
|
|
|
|
|
Otherwise |
|
|
An audit record is created, containing at least the following information: |
|
|
|
Table 22: Description of the Signing operation