1. Generate a key pair on the Utimaco HSM.
|
›_ Console |
|
|
Provide information when prompted.
Here:
-
ECis the key algorithm -
NONEis the key store for HSM -
CryptoServeris the store type -
123456is the slot PIN -
CryptoServeris the provider name -
tomsslec1is the key name that will be generated on the Utimaco HSM
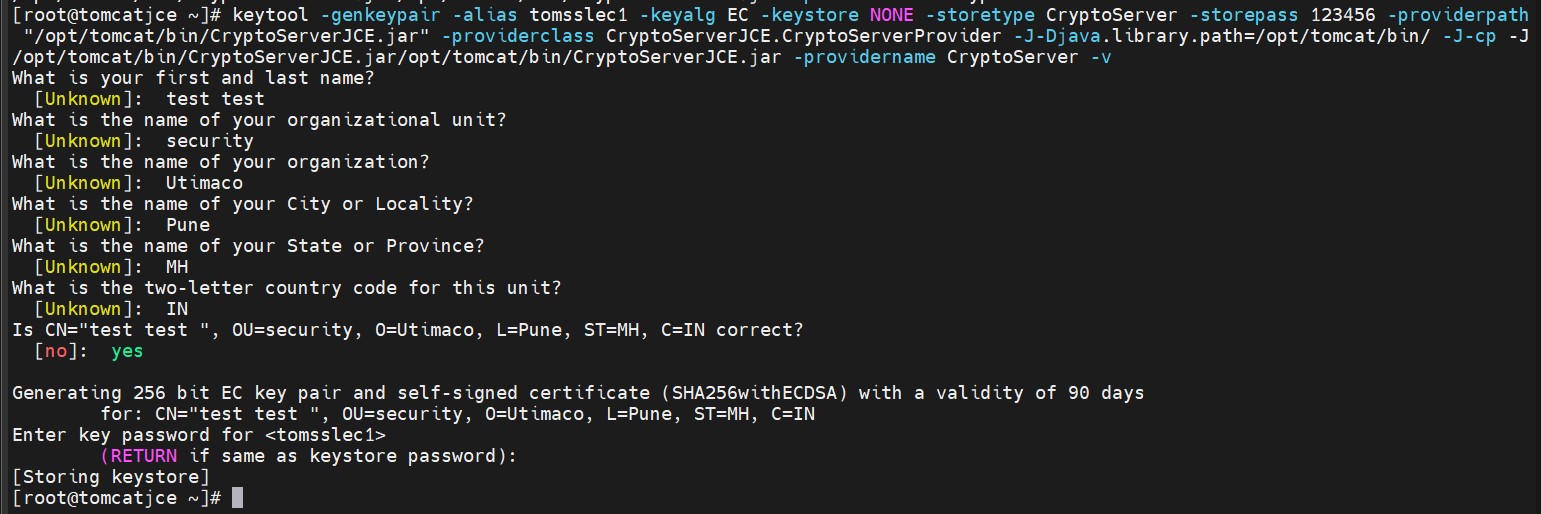
Key generation using the keytool command output
For OpenJDK 11 RSA key algorithm is not supported with Utimaco HSM.
2. Verify that the keys have been generated using the keytool command.
|
›_ Console |
|
|
Here:
-
NONEis the keystore for HSM -
CryptoServeris the store type -
123456is the PIN -
CryptoServeris the provider name
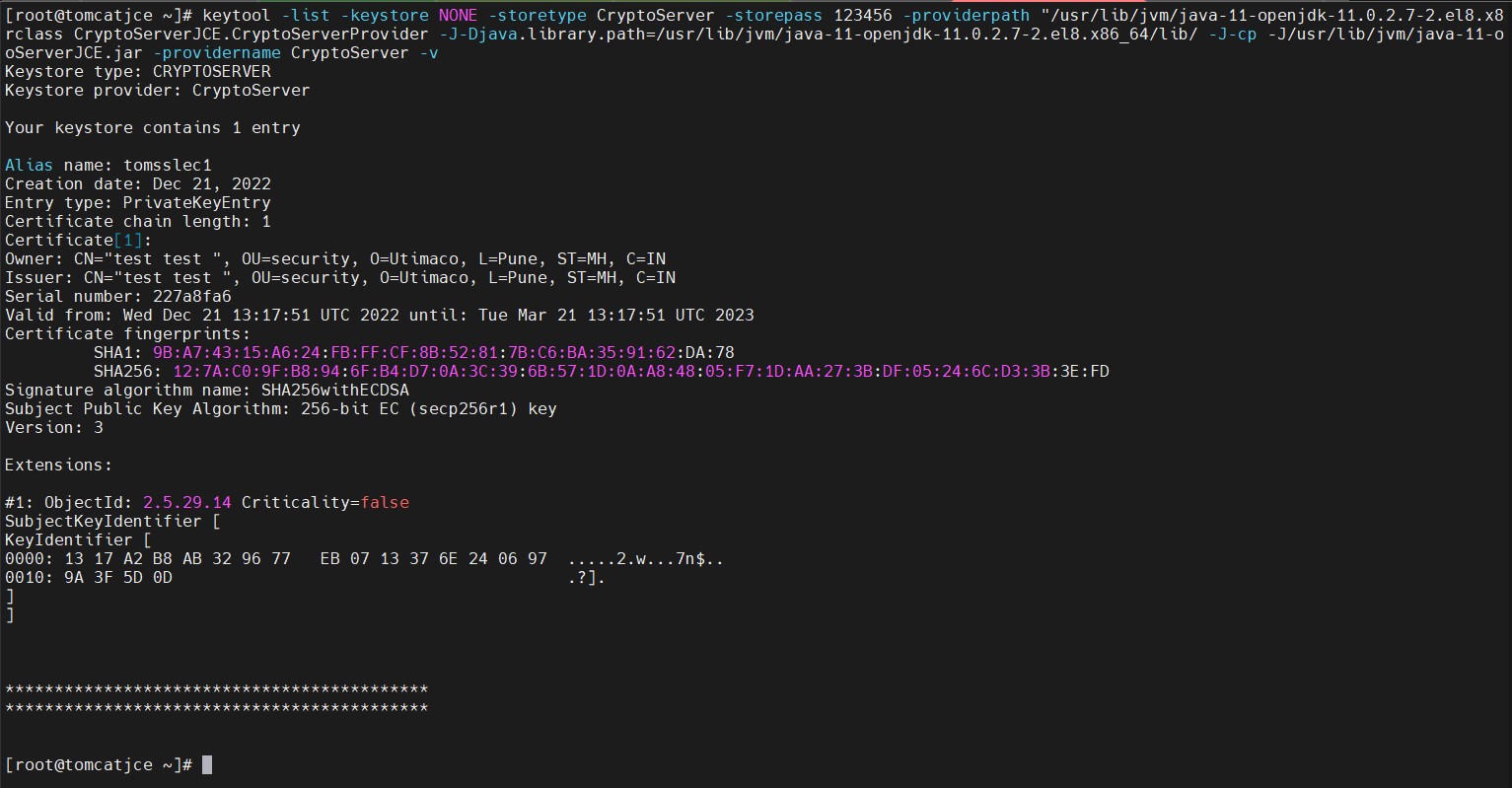
Keytool list output
-
List the keys using the cxitool.
|
›_ Console |
|
|
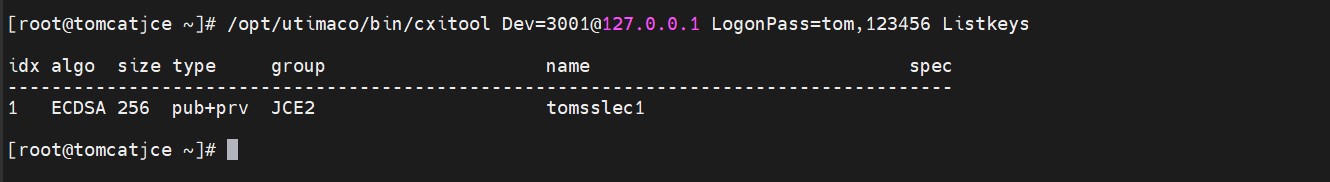
List keys output using cxitool
-
Generate a CSR using the
keytoolcommand
|
›_ Console |
|
|
Here:
-
tomsslec1is the key name -
NONEis the key store for HSM -
CryptoServeris the store type -
123456is the slot PIN -
CryptoServeris the provider name -
21dec.csris the CSR file name that will be generated
-
Get this CSR signed by the CA.
-
Copy the signed certificate along with the root CA certificate chain to the Tomcat server.
-
Import the signed certificate chain reply using the command below.
|
›_ Console |
|
|
Signed certificate must also contain certificate chain.
-
Verify that the
keytoolcommand shows the signed certificate as well as the root CA certificate.
|
›_ Console |
|
|
Here:
-
NONEis the key store for HSM -
CryptoServeris the store type -
123456is the slot PIN -
CryptoServeris the provider name
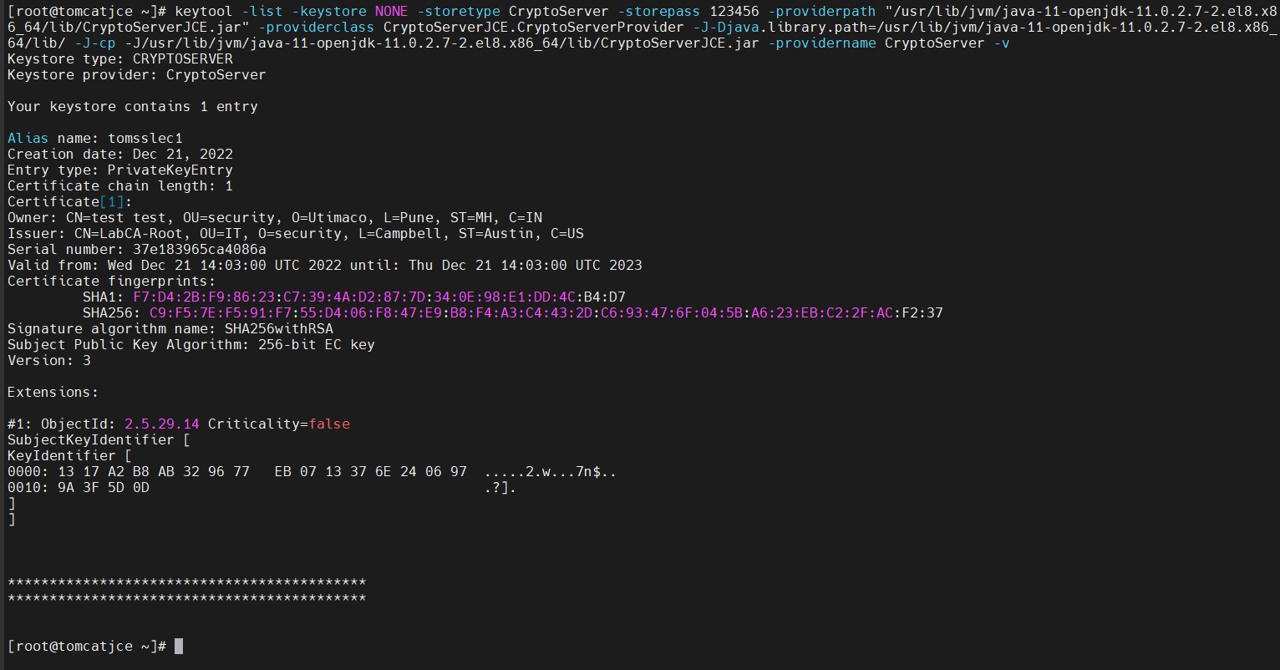
Keytool list output