-
Edit the vault server configuration at
/etc/vault/config.hclto add Utimaco HSM PKCS#11 library.
|
|
|
|
-
Restart the vault service.
|
|
|
|
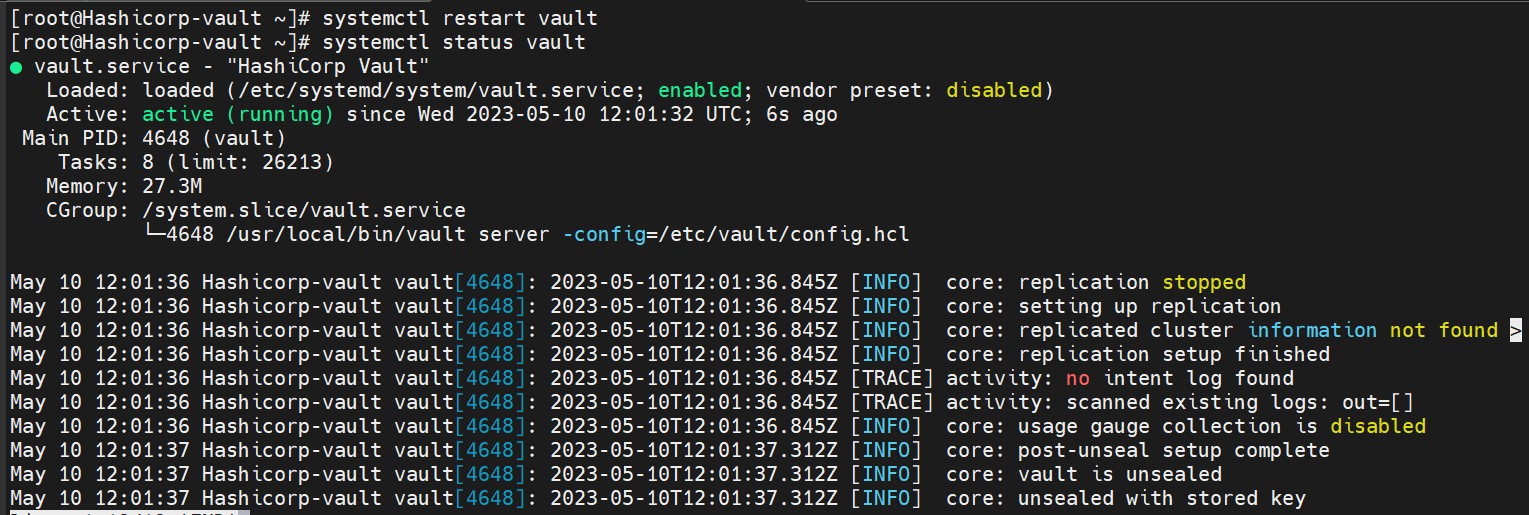
Vault service status
-
Log in to vault.
|
|
|
|
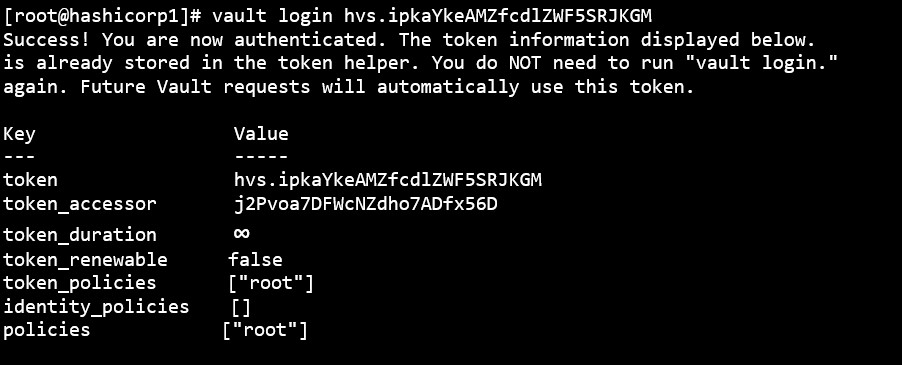
Login vault with root token
-
Each managed key requires the slot for key and a PIN to access and create the key on the HSM. Configure the managed key.
|
|
|
|
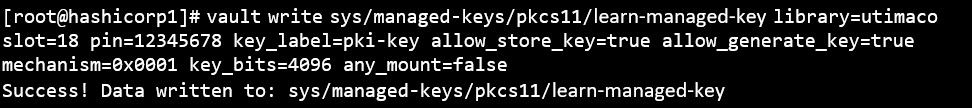
Configure the managed key
-
Read the key back.
|
|
|
|
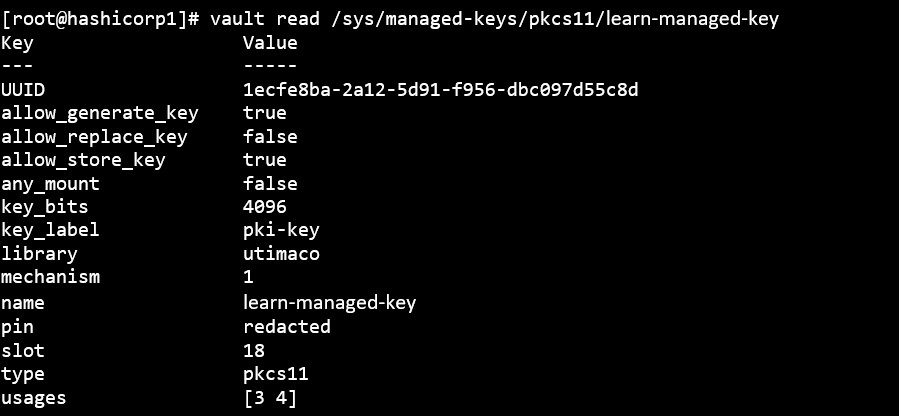
Key read
-
Test endpoint to validate that we can access the managed key.
|
|
|
|
The key has been generated in the HSM and used to sign and verify a dummy value.
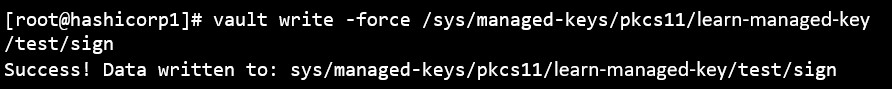
Sign managed key