There are different ways to access the code-signing certificate using Signtool.
-
The preferred method to do this is directly from the certificate stored with the thumbprint.
-
The second method is by using the key name
-
The third method is by pointing to a .cer file that was created by exporting the certificate.
In this guide an executable file called MyApplication.exe was created, signed, and timestamped.
1. Create a PowerShell script file with name Sign_Timestamp_Executable.ps1 and add the following content into the script file.
|
|
|---|
|
|
-
Launch PowerShell as Administrator and run
Sign_Timestamp_Executable.ps1. Enter the passphrase when prompted.
|
|
|---|
|
|
If you are using Smartcard Authentication, the prompt will go on the PIN Pad device to insert Smartcard and enter the pin. Then press OK button on the PIN Pad.
-
You can verify that your application is now signed by right clicking on it and selecting Properties. On the Digital Signatures tab (if it exists), you can view the signing certificate and timestamp.
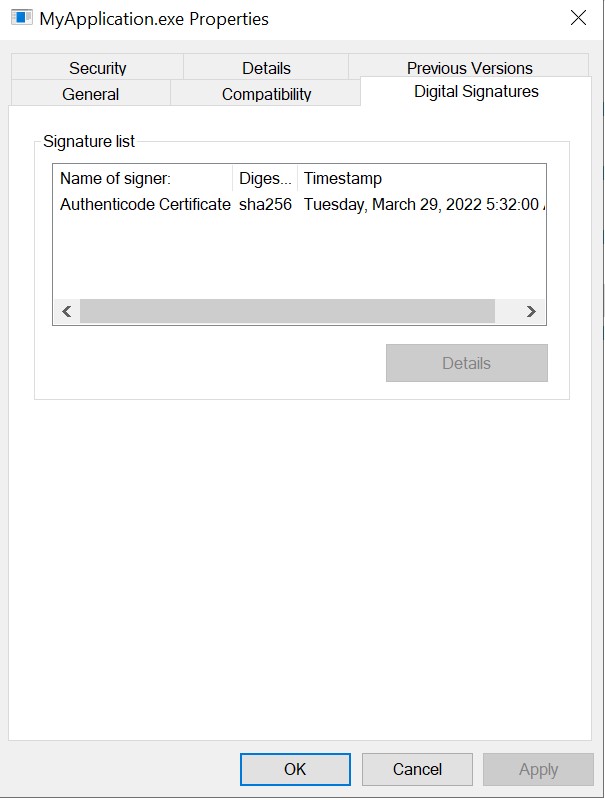
Digital signature details