-
Create a directory to generate the certificate request for sender and receiver
|
›_ Console |
|
-
Generate a sender key pair using p11tool2 For RSA
|
›_ Console |
|
For ECC
|
›_ Console |
|
Once key generation is completed then add CKA_ID for both public and private ECC keys using PKCS11# CryptoServer Administration tool.
-
Verify that the keys are generated onto the HSM using following command. For ECC
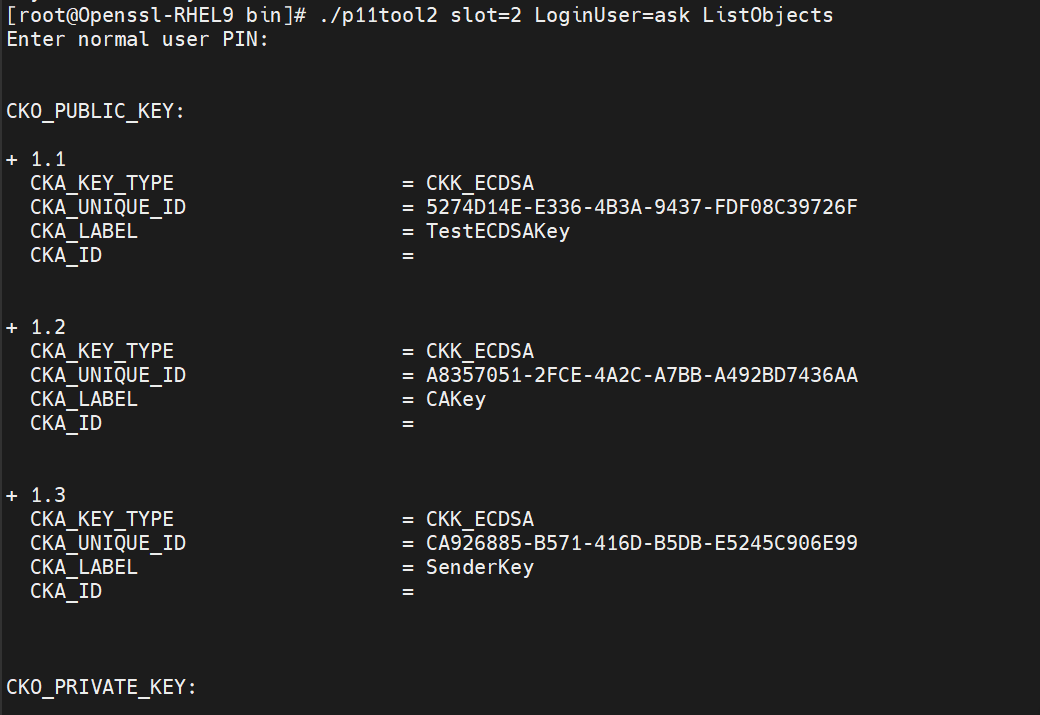
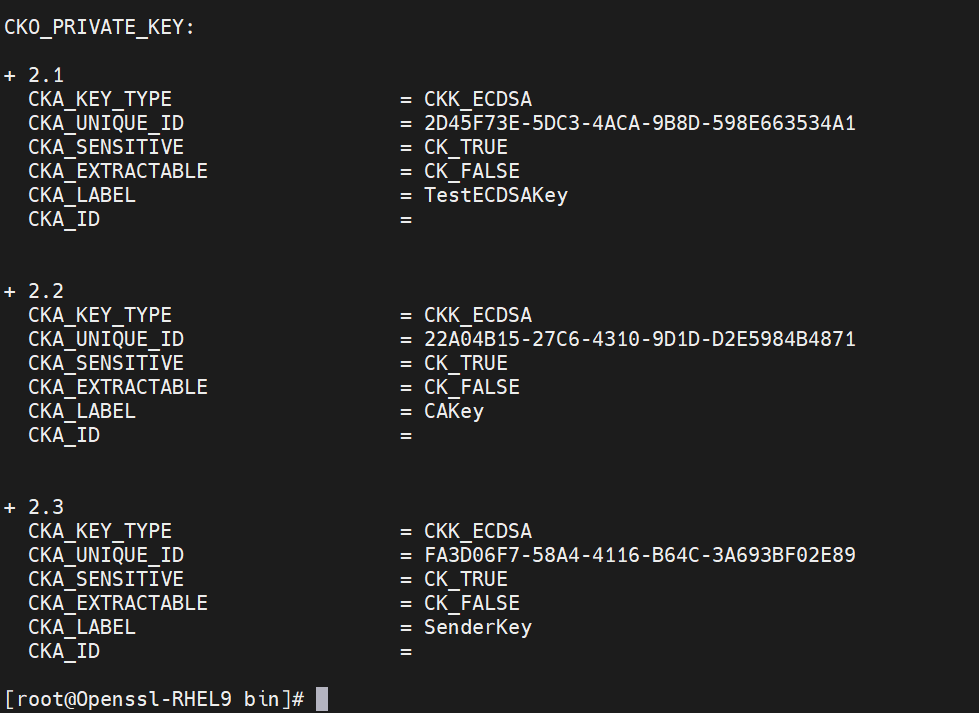
Figure 23: CA certificate generation output Sender ECC Key List
For RSA
|
›_ Console |
|
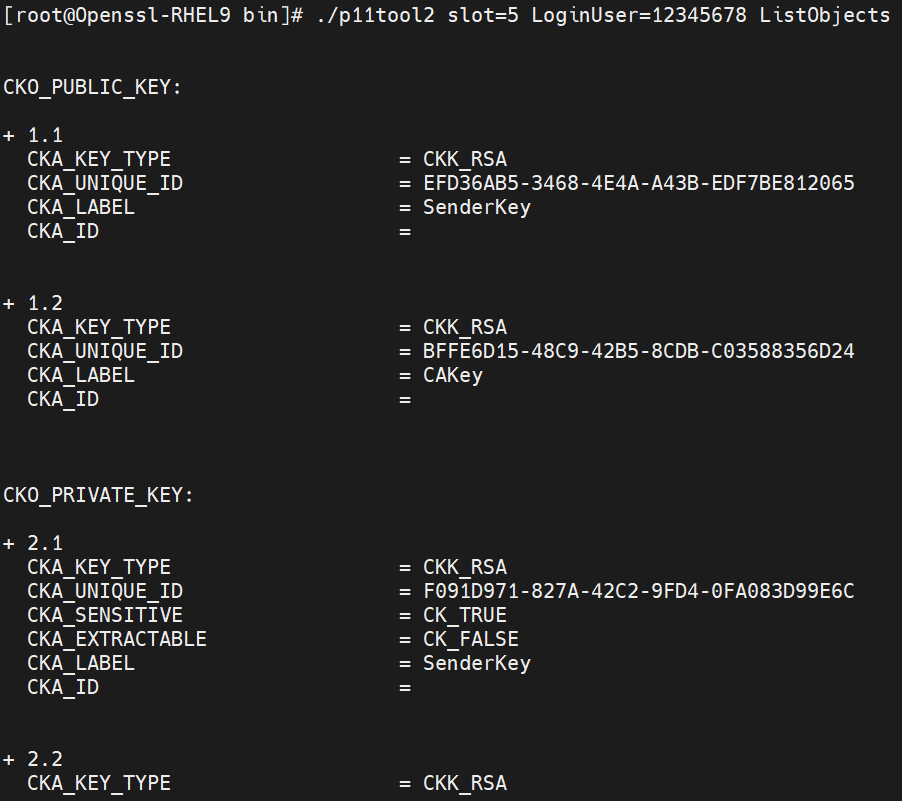
Figure 24: Sender RSA Key list
-
Generate a certificate request for sender.
|
›_ Console |
|
Figure 25: Sender certificate request generation
Enter the prompted value for "A challenge password" as blank.
Here SSLCert1 is the token label and SenderKey is the key on the HSM. Provide Cryptouser PIN when prompted.
-
Sign the certificate request for sender by CA
|
›_ Console |
|
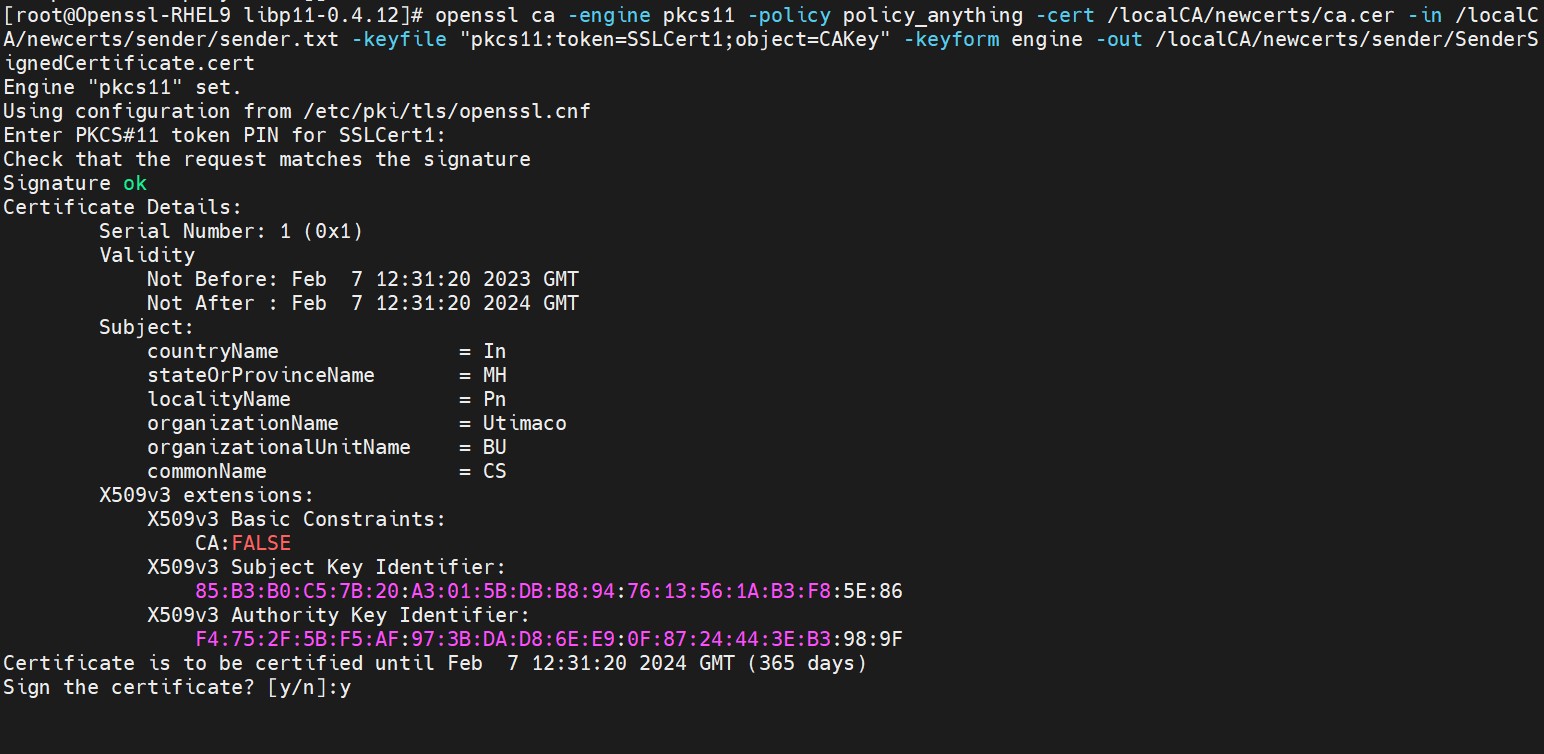
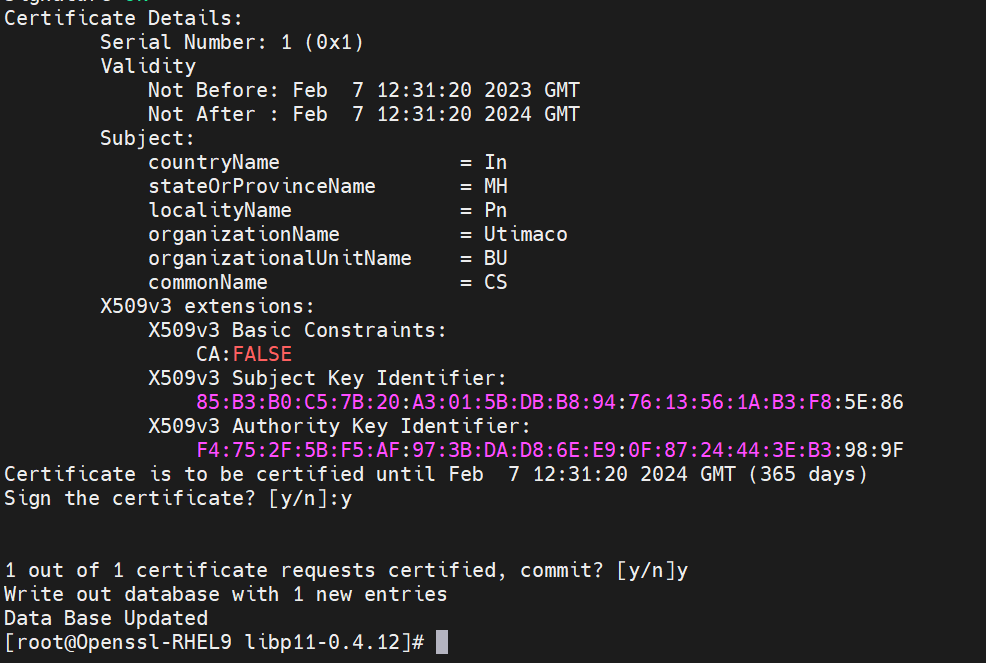
Figure 26: Sender certificate request signing by CA
Press y to sign and y again to commit.
Here SSLCert1 is the token label and CAKey is the key on the HSM. Provide Cryptouser PIN when prompted.
-
Generate key pair for receiver using p11tool2
For receiver only RSA keys are generated. OpenSSL 3 does not support encryption and decryption with ECC key.
For RSA
|
›_ Console |
|
Verify that key pair is generated onto the HSM using following command.
|
›_ Console |
|
For RSA
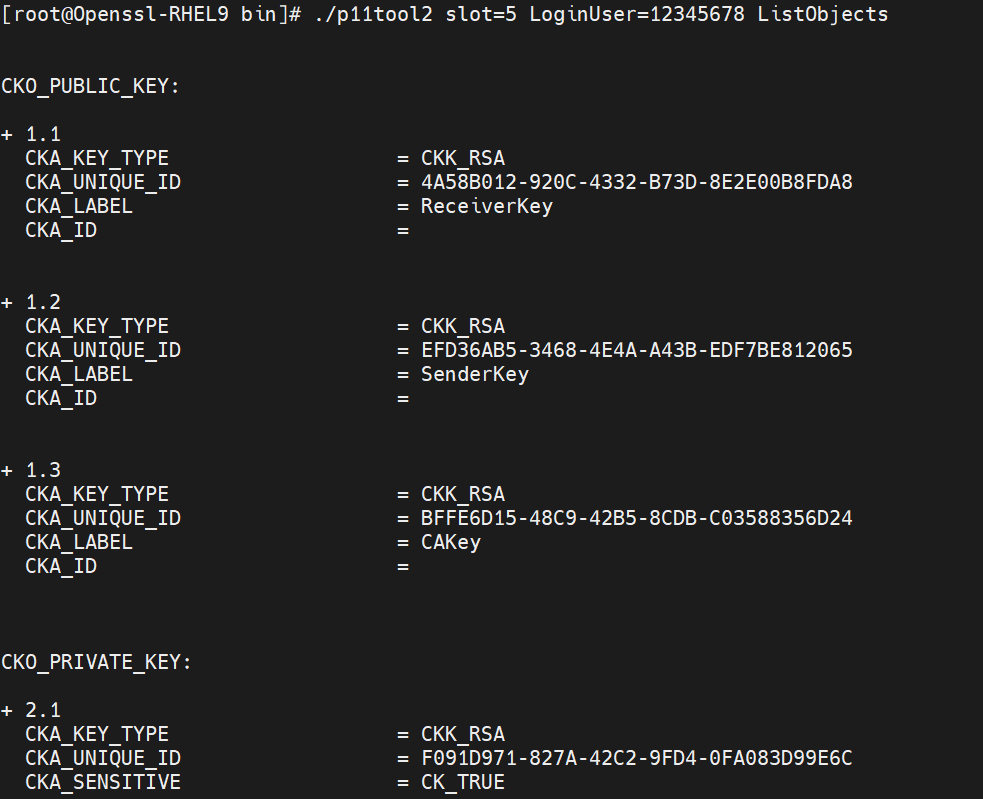
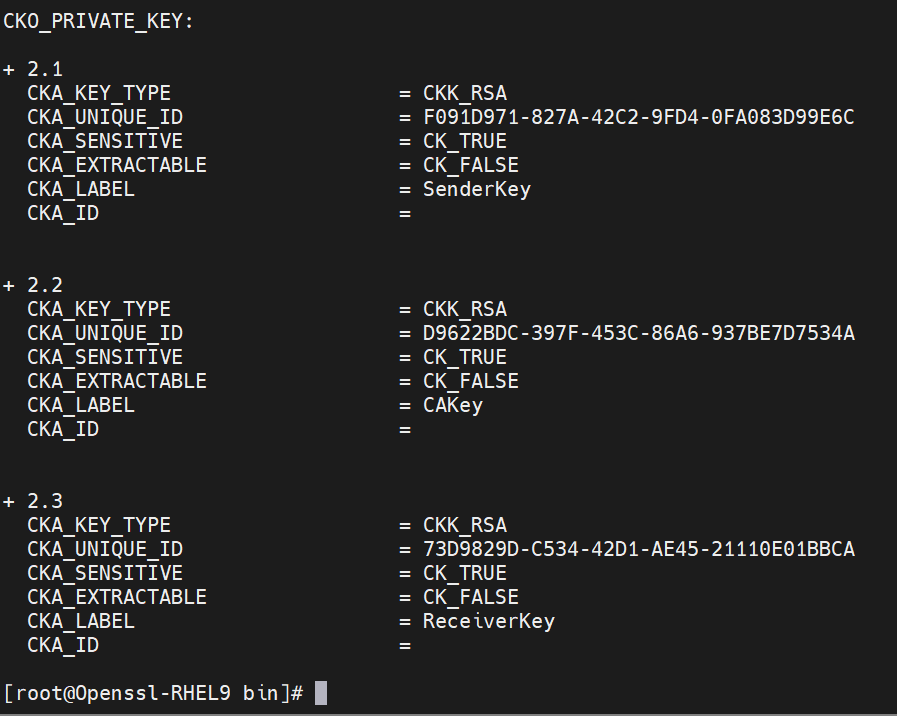
Figure 27: Receiver RSA Key list
-
Generate a certificate request for receiver
|
›_ Console |
|
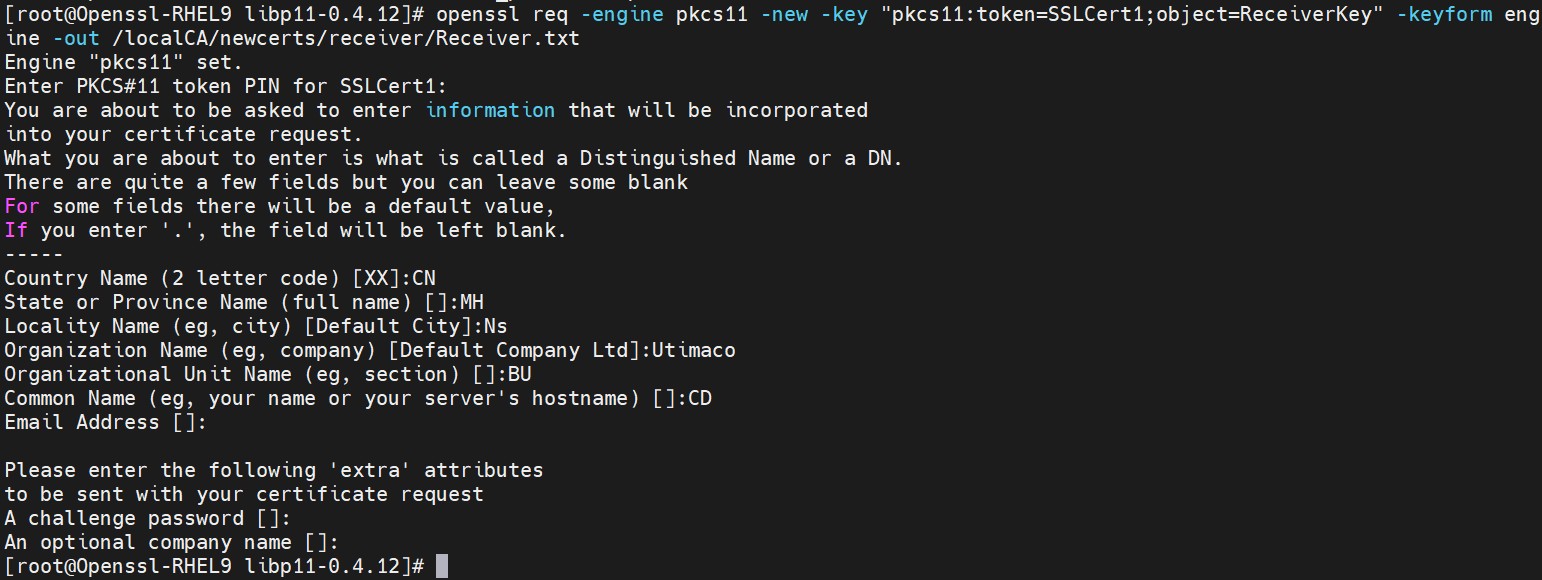
Figure 28: Receiver certificate request generation
Enter prompted value for "A challenge password" as blank.
Here SSLCert1 is the token label and ReceiverKey is the key on the HSM. Provide Cryptouser PIN when prompted.
-
Sign the certificate request for receiver by CA
|
›_ Console |
|
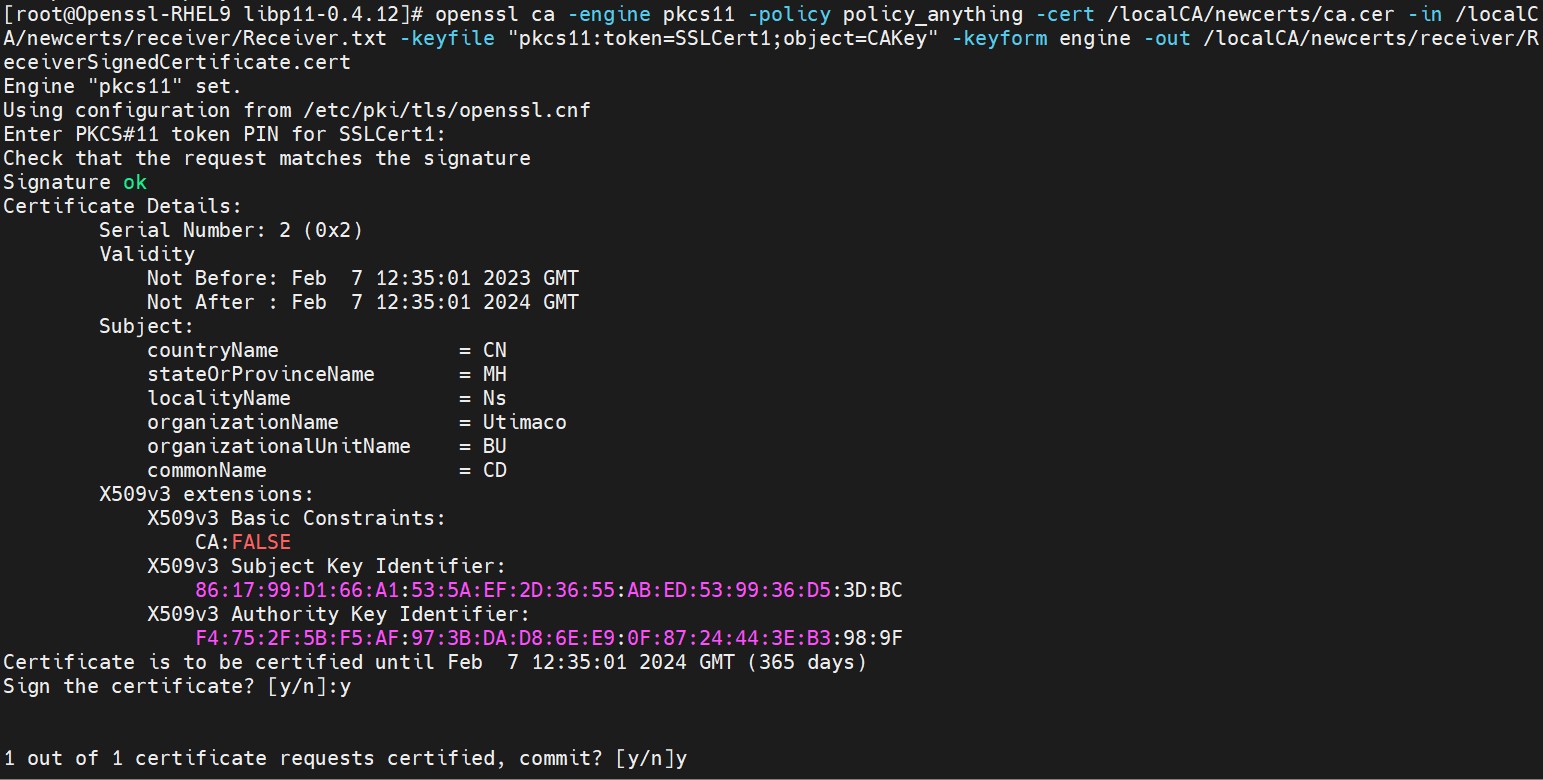
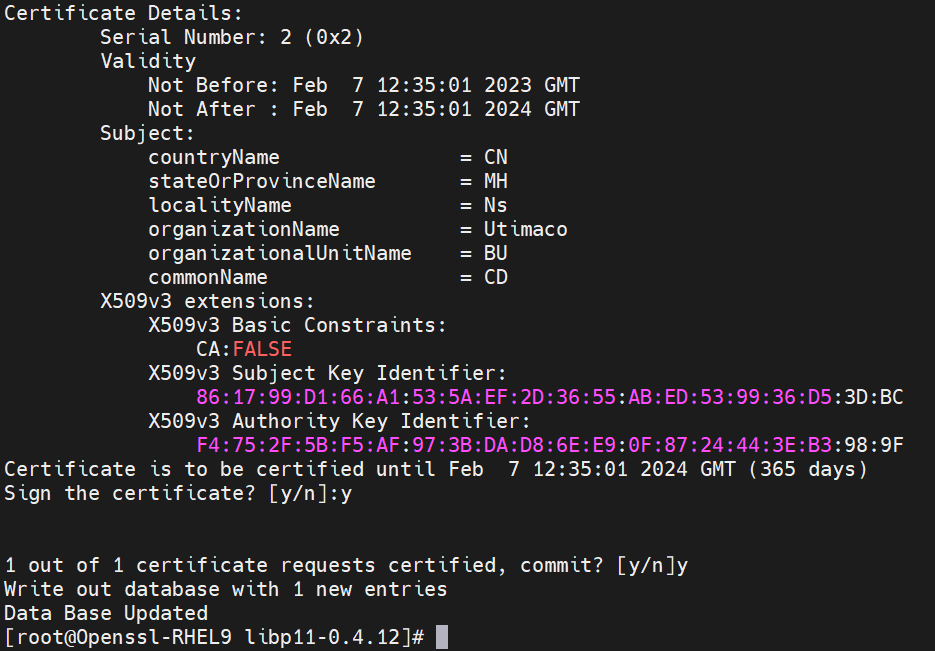
Figure 29: Receiver certificate request signing by CA
Press y to sign and y again to commit.
Here SSLCert1 is the token label and CAKey is the key on the HSM. Provide Cryptouser PIN when prompted.