-
Open the /< OPENSSLDIR>/openssl.cnf file in the text editor and edit the [CA_default] section to following
|
›_ Console |
|
new_certs_dir = $dir/newcerts
You can change dir to the directory of your choice, but make sure to use correct path in the subsequent steps. Here we have created directory /localCA under root directory and new_certs_dir= $dir/newcerts
-
Create the directory /localCA/newcerts
|
›_ Console |
|
-
Create the text files /localCA/index.txt and /localCA/serial
|
›_ Console |
|
-
Open the /localCA/serial file and write 01 in it and click enter. Save the file
-
Create a key pair by using p11tool2 for root CA For RSA
|
›_ Console |
|
This generates RSA 2048 CA private and public keys on the HSM For ECC
|
›_ Console |
|
This generates ECC CA private and public keys on the HSM
-
Verify that the RSA keys are generated onto the HSM using following command
|
›_ Console |
|
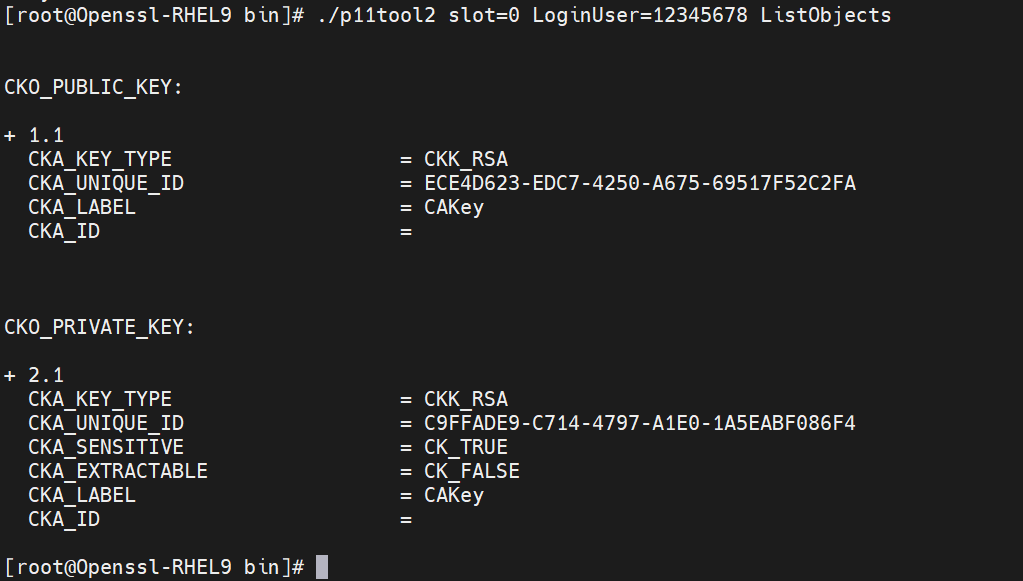
Figure 20: CA RSA Key list
-
Verify that the ECC keys are generated onto the HSM using following command
|
›_ Console |
|
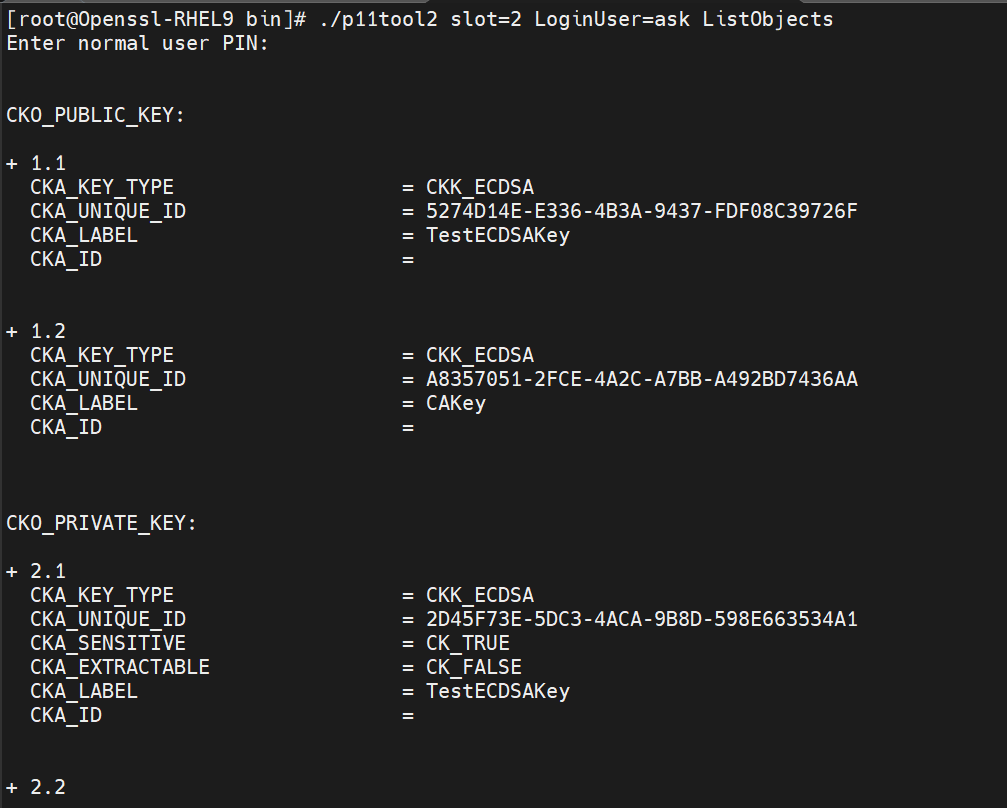
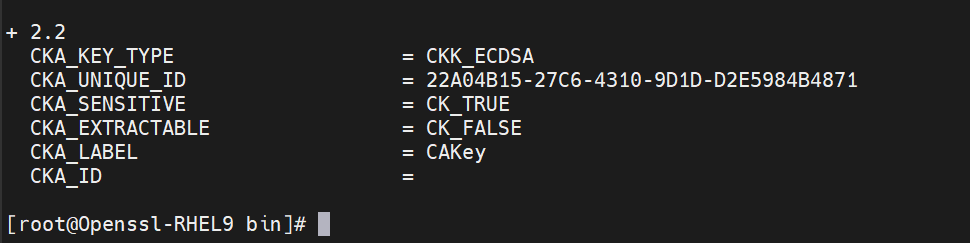
Figure 21: List ECC key
-
Create the CA certificate based on the generated key that is used for signing other certificates by running below command.
|
›_ Console |
|
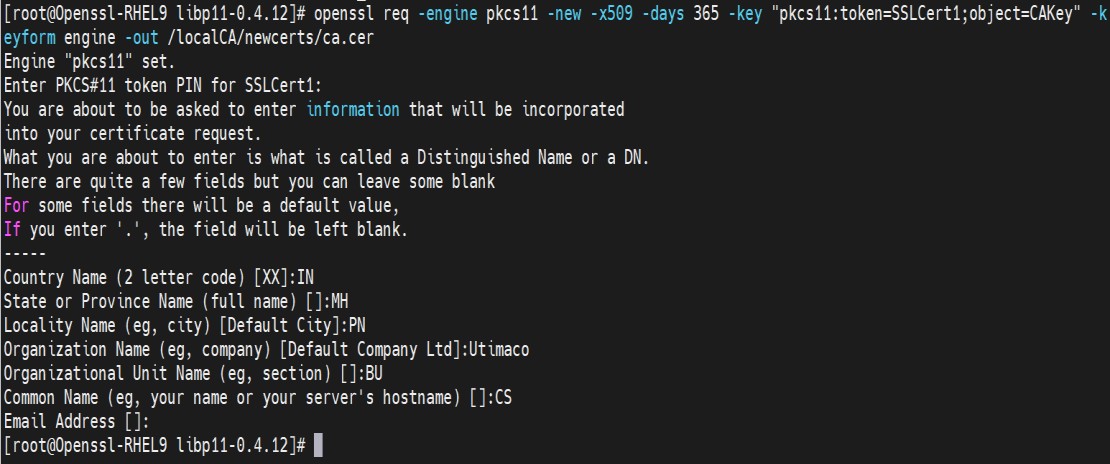
Figure 22: CA certificate generation output
Here CAKey is the Object label for the CA private key on the Utimaco HSM created in Step 5 and SSLCert1 is token label. Provide Cryptouser PIN when prompted.