-
Generate the ECC key using p11tool2
|
›_ Console |
|
Once key generation complete then add CKA_ID for both public and private ECC keys using PKCS11# CryptoServer Administration tool. Also make sure to set CKA_DERIVE=CK_TRUE in above command.
-
Verify that the keys are generated onto the HSM using following command
|
›_ Console |
|
Example
|
›_ Console |
|
-
Generate a certificate request
|
›_ Console |
|
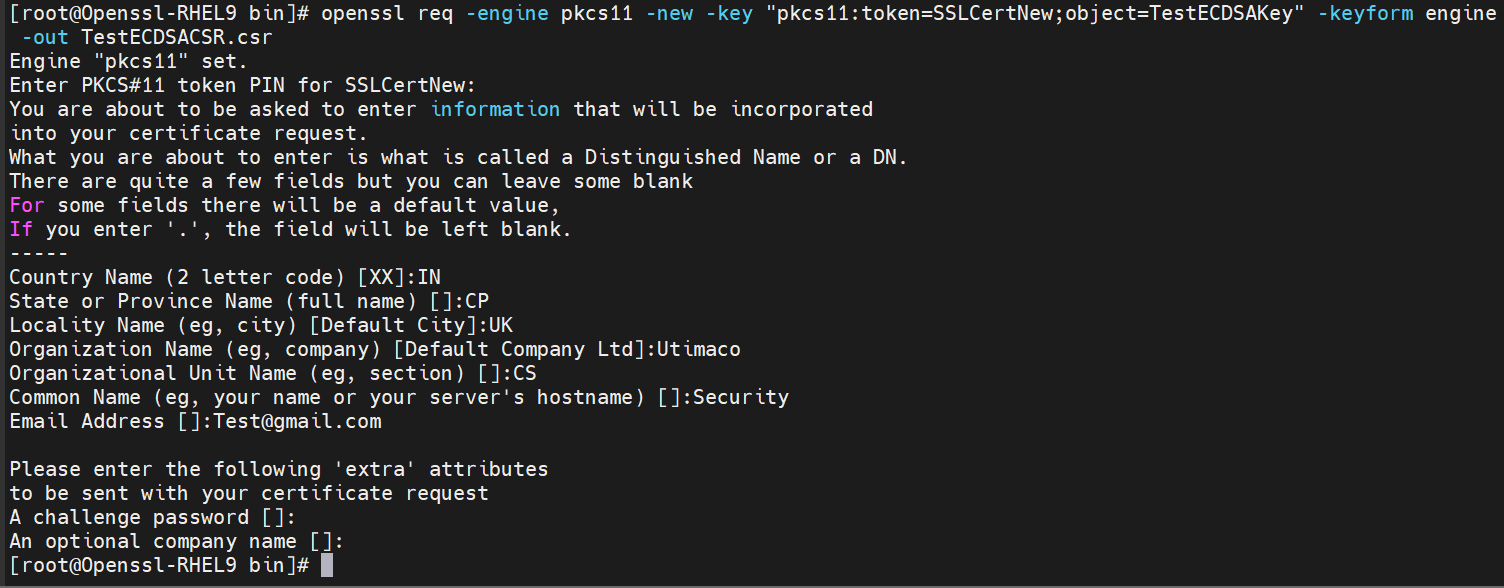
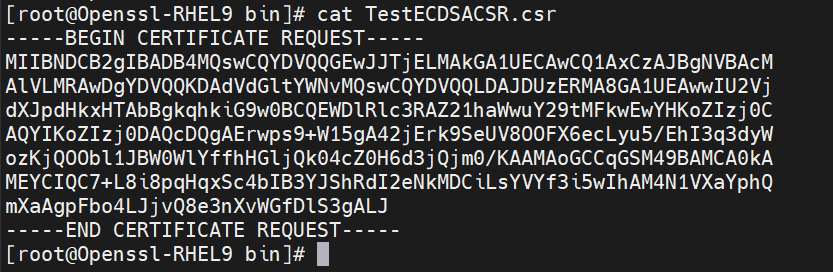
Figure 15: Generate certificate request and Content of generated certificate request
Here SSLCertNew is the token label and TestECDSAKey is the key on the HSM. Provide Cryptouser PIN when prompted.
-
Create a self-signed certificate based on the generated key
|
›_ Console |
|
Here SSLCertNew is the token label and TestECDSAKey is the key on the HSM. Provide Cryptouser PIN when prompted.
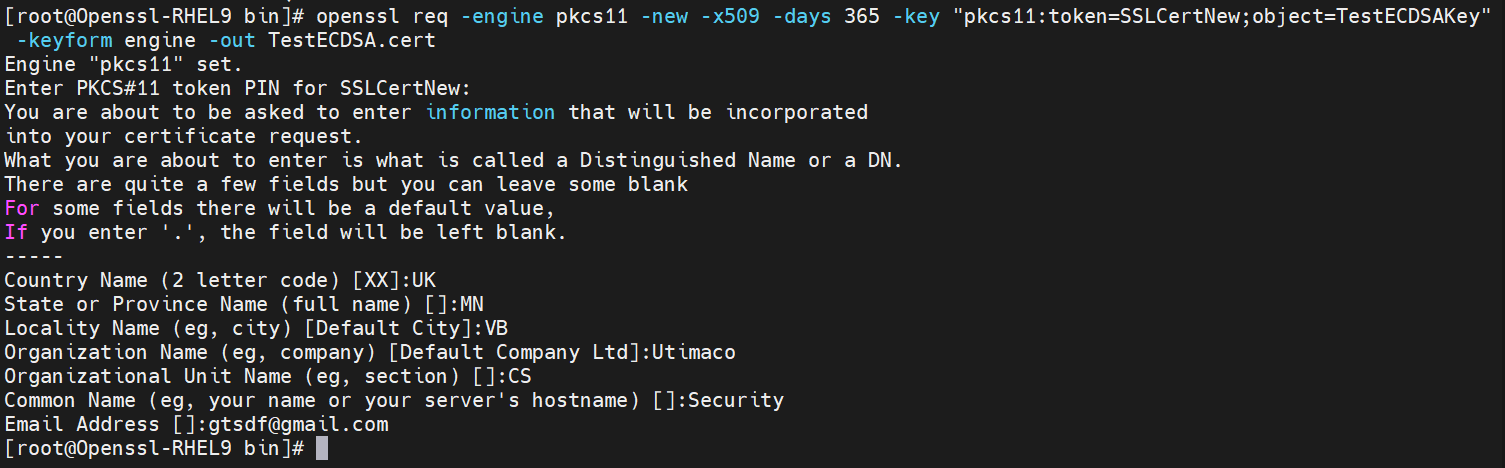
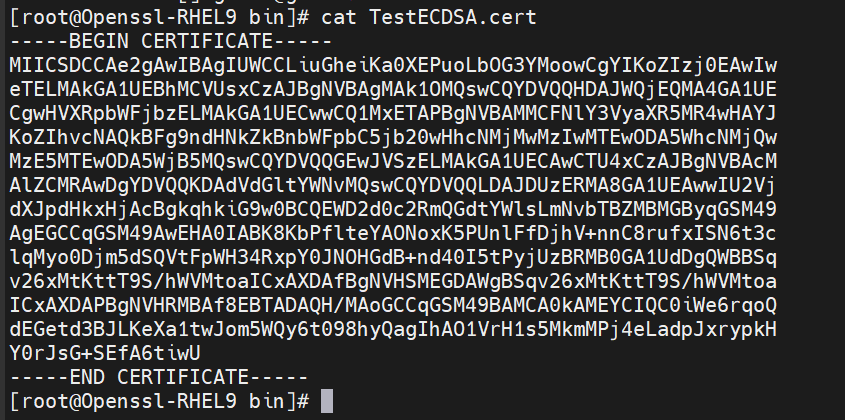
Figure 16: Content of self-signed certificate
-
Create a sample text file and write any content inside it
|
›_ Console |
|
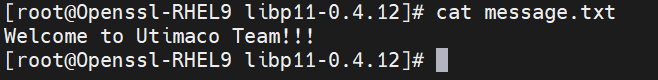
Figure 17: Content of message file
-
Sign the message file
|
›_ Console |
|
Here SSLCertNew is the token label and TestECDSAKey is the key on the HSM. Provide Cryptouser PIN when prompted.
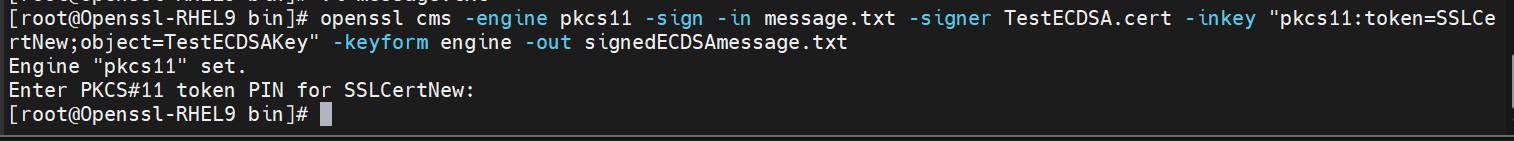
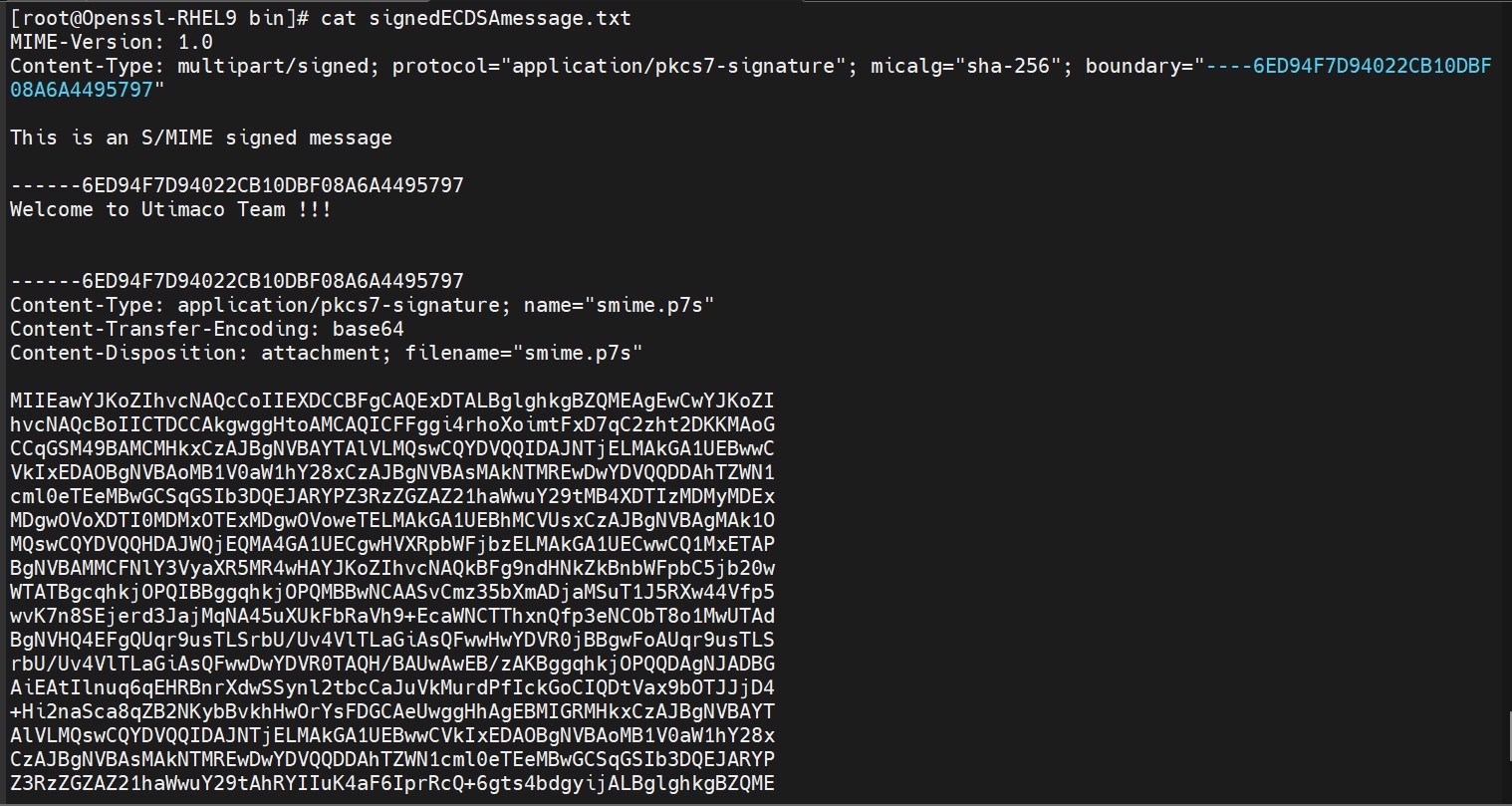
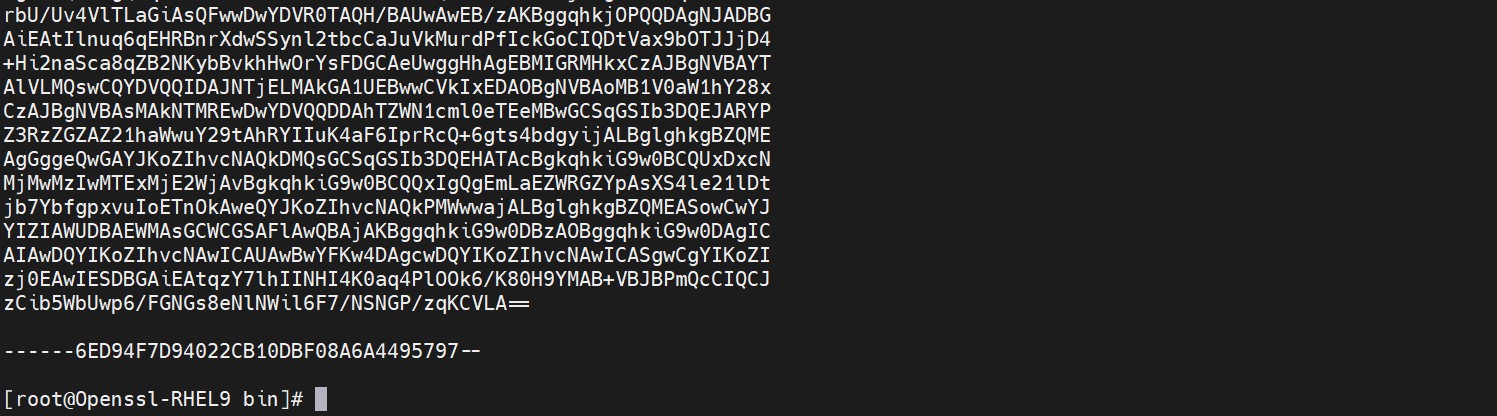
Figure 18: Content of signed message file
-
Verify the signed message file
|
›_ Console |
|
-
Open the content of originalmessage.txt and verify it is same as original content.
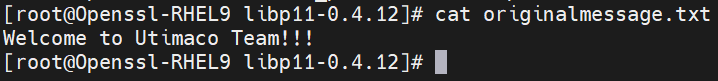
Figure 19: Content of original message file