Configuration on Utimaco CryptoServer GP HSM
-
Create users SO (Security Officer) and USR (the Crypto user) and initialize a slot. This is done using p11tool2. We first create the SO using the InitToken command and then the USR using the InitPin command.
|
›_ Console
|
|
# ./p11tool2 Slot=<slot no.> Label=BarbicanToken Login=ADMIN,ADMIN_CP5.key InitToken=<SO pin>
# ./p11tool2 Slot=<slot no.> LoginSO=<SO_pin> InitPin=<CryptoUser_PIN>
|
-
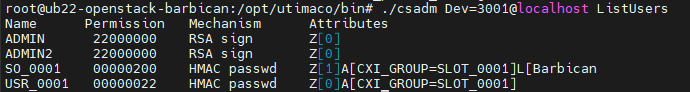
Run the csadm ListUsers command to see the created users.
Security officer and cryptographic user created
-
Export the HSMs mutual authentication key. The port@address is 3001@localhost if running the simulator locally. Hardware HSM will have the port 288 (288@address).
|
›_ Console
|
|
# cd /opt/Utimaco/bin
# ./csadm dev=<port@address> GetHSMAuthKey > /opt/utimaco/HSMAuthKey.key
# cat /opt/utimaco/HSMAuthKey.key
CS000000=0601020180000180A9611F90A8377FDFC90BC3097556F5873EFE31F9F697E44AA7C81A91FDCD9154D84EDDCDF53340E8891D7E79F445ECEFFEE1FBF6C014E054E1787C43816A6C8D1E1C75C44F534F890B57CF3A876CC47C68C5CE8D5C0EA05D9E6FBED4AD7C2905BC2527D832C67CE298B7946B0A10FA23048A74D91D1EBA487DFDDAF4AE0B9EA25AC3213EB7874AE8700A18D36A20C9A915A2A1216DEEBA872FB296DDF28587ADF805CDEC7A63178C2F25956AB1B9037D4A8774273E6A3CBBF5CA90221EAC91211AB1E848DB0A26A4B94AF5F835B8DA0B01E17759CC0A746FA834FEBAE24604228C7AF8442FA651FC9ED8545C23D5BF313D3DBD9D662B9B3162A4D42CC4B3F4F3E73B57475836B7A89A228E3F9793A488031E2D09AB48F06ABEEA18618CDB6BFFE7C2D370F7C1AEF3C1B03E53D73E45CE58B3CEB81C514FFA691FBA087D6C24E31DC17123B3B4DF2880CE44E278DBF8A23B35A7FEC9228808F560F062DA984B0A65B6ACB7AB1A0EC716A1F31268039CA4DC37B4DDBC989AF4C15723B8364758D95554494D41434F204353303030303030018099DEC18B5179B5A8FE0F88AA24D57A272584A4221B591AC3D513093763597E2A5F153D72AD896C24A57509D5FC21D8F1ABD621825A18B2D9497857C5169C0A2286CA334986113A23A5B3D786C711824F98C764AD0C3AF6A45FE0823363BE3D7ACD2CD0308BD4EB36879136F0A12BDD8C13EE58869DFAA24596C4BDA8436D3BE259F5E25A0EC3D1E3CF38F92969D7A65F709049B95DB3546E5740EAA28F0F8D960AE4A243C6380C091D7BC1773C50EC88B1CC4D9705D99DD8DA4D7164903F7A9B76BB73C488B003F41BE2A1A4DF3C13229DD69D64E7B50D7C6624BAA2611E8198990BA502D33CF21472A57659E8B728FAC25B8B9113921854878802C00BA083EDC0D910CD93655ED2004010D38CCE6B43D72564559F7CBA7212EE28EA5DF63174B937918BC65365046F5C9DCF4121A3ED711E3D037C6655BD99939B4BF80F795CB0F755DCCD2627225CF6C76ADC61580EA98EE32ADE63E518C032BC36A44B939BD0C035573FDF1110B3B701883CD8FD2D8D8D36E882BB6292DDC40A54F2A5B5CD
#export CS_AUTH_KEYS=”/opt/utimaco/HSMAuthKey.key”
|
You can also add the above variable in users .bash_profile to make it persistent through multiple session.
|
›_ Console
|
|
# echo 'export CS_AUTH_KEYS="/opt/utimaco/HSMAuthKey.key"' >> ~/.bashrc
|