-
Generate the MKEK using the
p11tool2 GenerateKeycommand below.
|
|
|
|
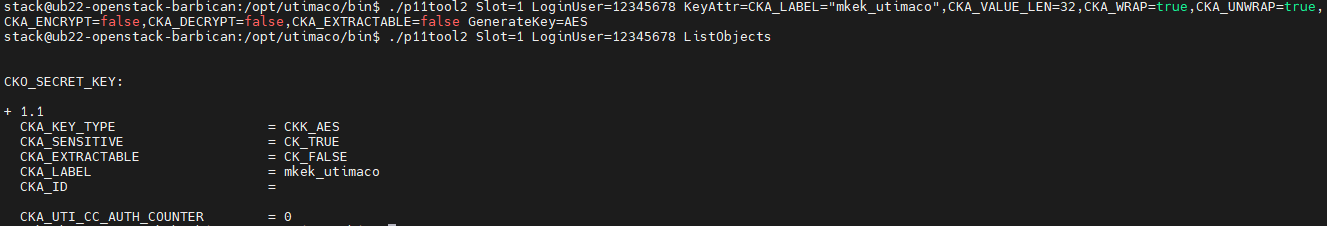
MKEK generation
Barbican can be used to generate an MKEK. However, using barbican-manage hsm gen_mkek causes a key property invalid in CC mode error when attempting to create the key. The reason for that is that when HSM is operated in CC mode (which is the case for CryptoServer CP5), a key can not be used for both encryption/decryption and wrapping/unwrapping. The command adds the CKA_ENCRYPT and CKA_DECRYPT usage flags to the key. To work around this issue, the key is created with custom attributes using the p11tool2 with CKA_ENCRYPT and CKY_DECRYPT set to false as the key is only required for wrapping/unwrapping.
-
Generate the HMAC using the
barbican-manage hsm gen_hmaccommand.
|
|
|
|
HMAC generation
-
Verify that the keys are generated on the Utimaco HSM using the
p11tool2 ListObjectscommand.
|
|
|
|
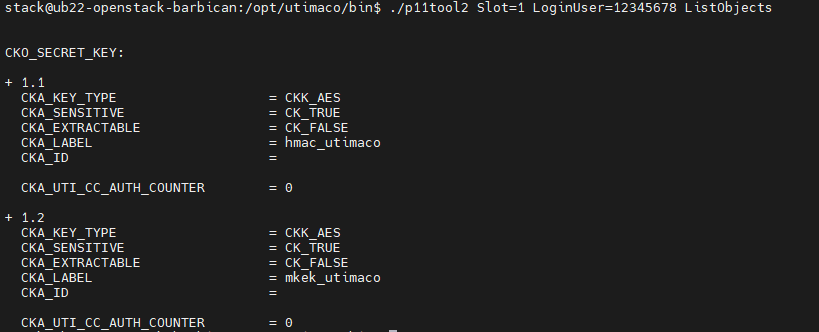
Listing HMAC and MKEK with p11tool2