KEK Rewrap Compatibility
In OpenStack Barbican Dalmatian, the PKCS#11 unwrap_key() interface requires an explicit encryption mechanism parameter, while the rewrap_pkek utility still uses an older call signature. Without alignment, KEK rewrapping fails. A small compatibility fix is required to pass the configured encryption mechanism to unwrap_key().
The compatibility fix is performed with the following steps:
-
Locate the pkcs11_kek_rewrap.py script (default location is
/opt/stack/barbican/barbican/cmd/pkcs11_kek_rewrap.py). -
Find the original code.
|
|
|
|
-
Update the code.
|
|
|
|
-
Save the changes.
Perform the key rotation using the following steps:
-
Generate a new MKEK using the
p11tool2 GenerateKeycommand below.
|
|
|
|
New MKEK generated
-
Generate a new HMAC using the
barbican-manage hsm gen_hmaccommand.
|
|
|
|
New HMAC generated
-
Verify that the keys are generated on the Utimaco HSM using the
p11tool2 ListObjectscommand.
|
|
|
|
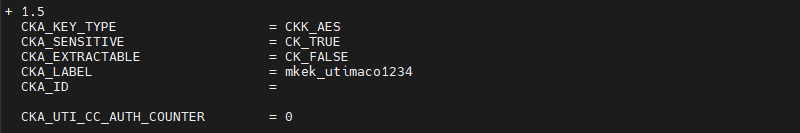
Listing keys with p11tool2 (MKEK)
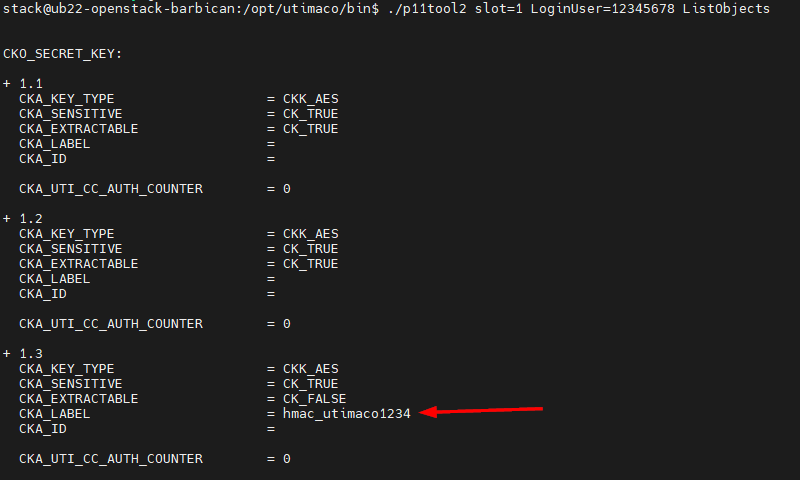
Listing keys with p11tool2 (HMAC)
-
Initialize and authorize the new keys using the procedure described in Initialize and Authorize HMAC and MKEK for CP5. The same authorization key
KA.keycan be used. -
Open barbican.conf and change the ‘mkek_label’ and ‘hmac_label’ values to the labels of keys created in previous steps.
|
|
|
|
-
Restart OpenStack Barbican services.
|
|
|
|
-
Run rewrap_pkek command to rewrap PKEK with the new MKEK.
|
|
|
|
Rewrapping PKEK
-
Verify that you can get value of the secret generated earlier.
|
|
|
|
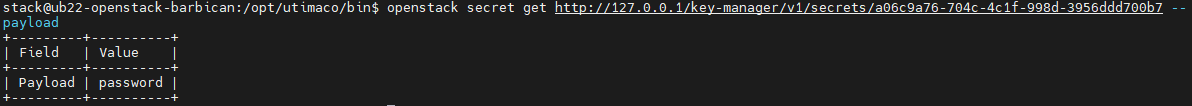
Fetching secret's value after PKEK rewrap