-
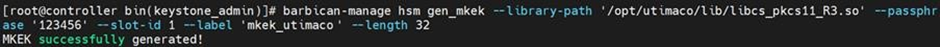
Generate the MKEK using the below command.
|
|
|
|
-
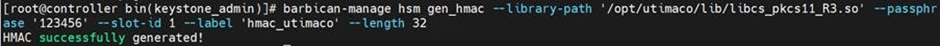
Generate the HMAC Key using the below command.
|
|
|
|
-
Verify that the keys are generated on the Utimaco HSM using the p11tool2 command.
|
|
|
|
-
Restart the OpenStack-Barbican-API and httpd services.
|
|
|
|