Use the steps below to rotate the keys.
-
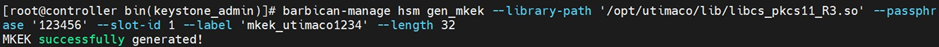
Create a new MKEK Key by using the command below.
|
|
|
|
-
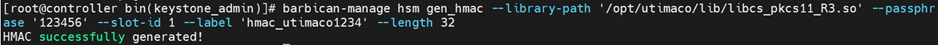
Create a New HMAC Key by using the below command.
|
|
|
|
-
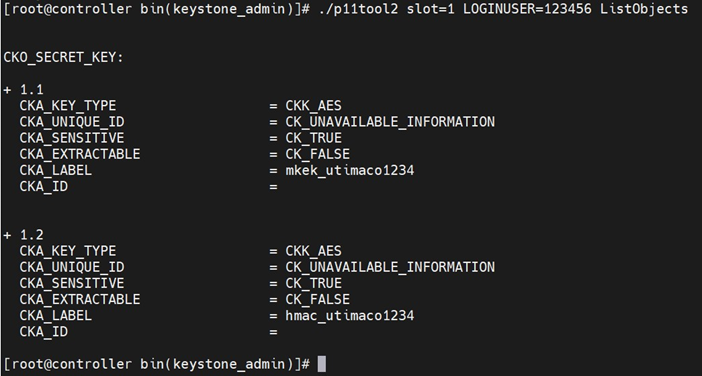
Verify that the keys are generated on the Utimaco HSM using the p11tool2 command.
|
|
|
|
-
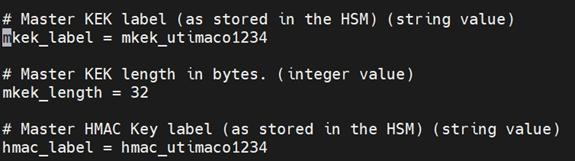
Add a new label to the Barbican config file.
-
Restart OpenStack-Barbican-API and the https service.
|
|
|
|
-
Run the rewrap_pkek command to rewrap pkek with the new mkek.
|
|
|
|
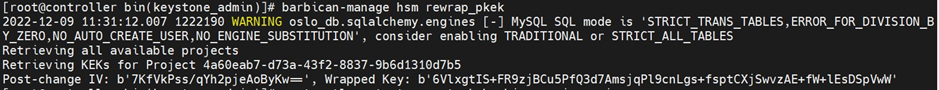
-
Restart the OpenStack-Barbican-API and httpd services.
|
|
|
|
-
Verify that you can get the secret generated earlier.
|
|
|
|
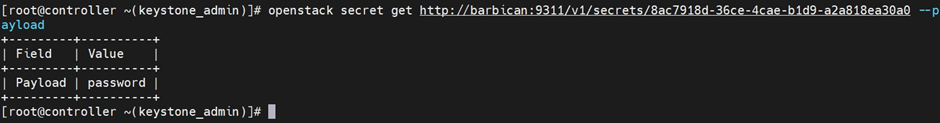
This completes the integration of OpenStack Barbican and Utimaco HSM.