KEK Rewrap Compatibility
In OpenStack Barbican Flamingo, the PKCS#11 unwrap_key() interface requires an explicit key wrap mechanism parameter, while the rewrap_pkek utility still uses an older call signature. Without alignment, PKEK rewrapping fails. A small compatibility fix is required to pass the configured key wrapping mechanism mechanism to unwrap_key().
The compatibility fix is performed with the following steps:
-
Locate the
pkcs11_kek_rewrap.pyscript (default location is/opt/stack/barbican/barbican/cmd/pkcs11_kek_rewrap.py).
-
Find the original code.
|
|
|---|
|
|
-
Update the code.
|
|
|---|
|
|
-
Save the changes.
Perform the key rotation using the following steps:
-
Create a new MKEK using the
barbican-manage hsm gen_mkekcommand.
|
|
|---|
|
|
Rewrap MKEK generated
-
Create a new HMAC using the
barbican-manage hsm gen_hmaccommand.
|
|
|---|
|
|
Rewrap HMAC generated
-
Verify that the keys are generated on the Utimaco HSM using the
p11tool2 ListObjectscommand.
|
|
|---|
|
|
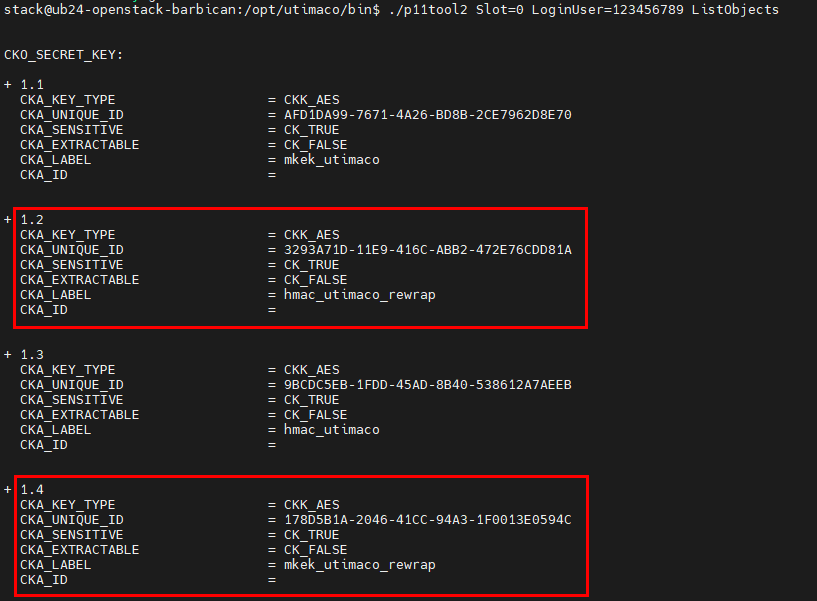
Listing rewrap keys with p11tool2
-
Edit the
barbican.conffile located in/etc/barbicanusing your preferred text editor and change themkek_labelandhmac_labelparameter values to the labels used when creating the new MKEK and HMAC.
|
|
|---|
|
|
-
Restart OpenStack Barbican service.
|
|
|---|
|
|
-
Optional: Run the
rewrap_pkekcommand with--dry-runoption to display the changes that will be made.
|
|
|---|
|
|
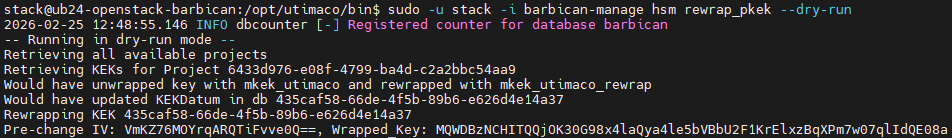
Rewrapping PKEK (dry run)
-
Run the
rewrap_pkekcommand to rewrap PKEK with the new MKEK.
|
|
|---|
|
|
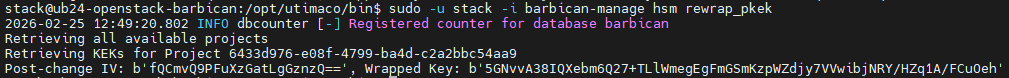
Rewrapping PKEK
-
You can verify the rewrap operation logging in the PKCS#11 log file
cs_pkcs11_R3.log.
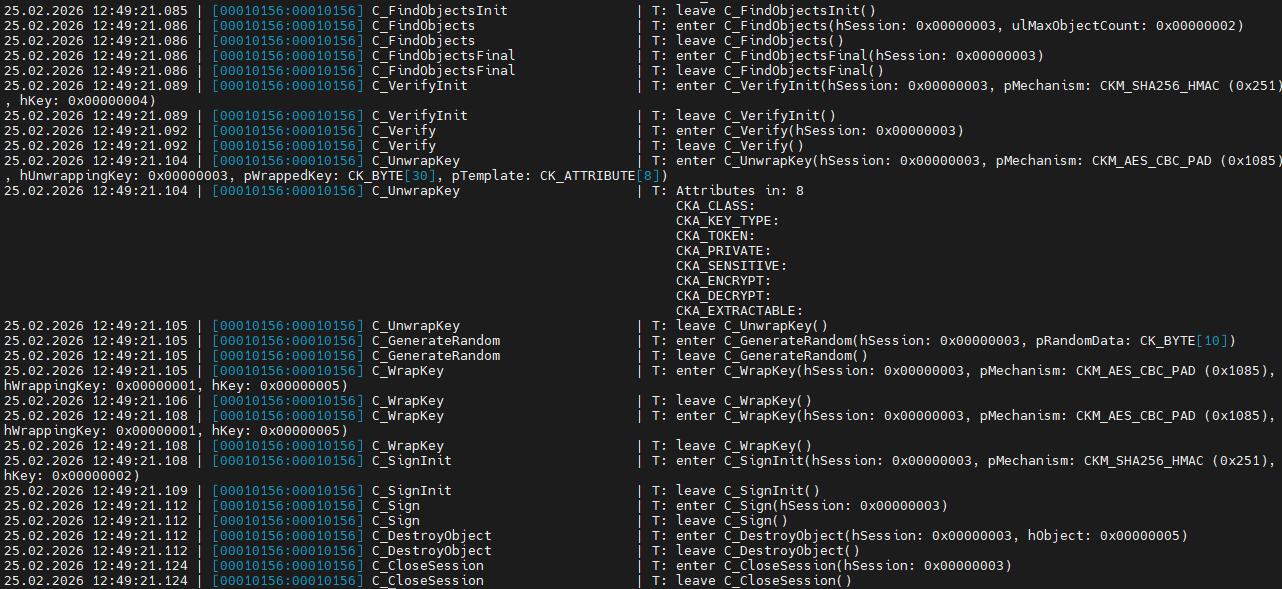
PKEK rewrapping in PKCS#11 logs
-
Verify that you can retrieve the payloads of the secrets generated earlier.
|
|
|---|
|
|
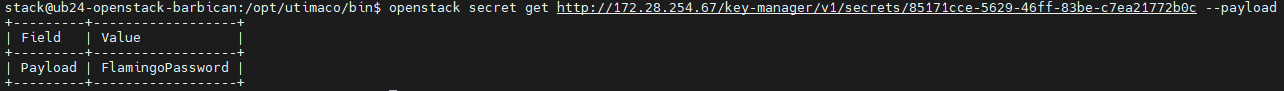
Retrieving secret value after PKEK rewrap