This step defines a Job that automatically generates an RSA key pair inside the Utimaco HSM during deployment. The key generation process is securely performed using the Utimaco PKCS#11 library, ensuring that the private key never leaves the HSM boundary. The same Job also generates a self-signed SSL certificate using the HSM key and stores it in an OpenShift Secret, which will later be mounted into the NGINX pods for SSL/TLS operations.
-
The Label (RSAKey) used in this Job must match the key label referenced in your NGINX ConfigMap (
ssl_certificate_key "engine:pkcs11:pkcs11:object=RSAKey;type=private";). -
Ensure that the Utimaco ConfigMap (
cs_pkcs11_R3.cfgandopenssl.cnf) has been created and applied before running this Job. -
Update the LoginUser (PIN) and HSM connection details in your configuration according to your environment setup.
-
Create a file named
key-generation.yamlunder the directory/home/admin/hsm-build/. -
Paste the following content into the file and save it.
YAMLapiVersion: batch/v1 kind: Job metadata: name: key-generator-job spec: template: spec: serviceAccountName: key-generator-sa volumes: - name: utimaco-cfg-volume configMap: name: utimaco-config - name: cert-volume emptyDir: {} containers: - name: key-generator image: <docker_username>/utimaco-sidecar:1 command: ["/bin/sh", "-c"] args: - > /opt/utimaco/bin/p11tool2 slot=0 LoginUser=12345678 Label="RSAKey" DeleteObject || true; /opt/utimaco/bin/p11tool2 slot=0 LoginUser=12345678 PubKeyAttr=CKA_LABEL="RSAKey" PrvKeyAttr=CKA_LABEL="RSAKey" GenerateKeyPair=RSA; openssl req -engine pkcs11 -new -x509 -days 365 -key "pkcs11:object=RSAKey;type=private" -keyform engine -out /certs/tls.crt -subj "/CN=test.utimaco.com"; oc create secret generic ssl-cert --from-file=tls.crt=/certs/tls.crt; oc create secret generic ssl-cert --from-file=tls.crt=/certs/tls.crt --dry-run=client -o yaml | oc apply -f -; volumeMounts: - name: utimaco-cfg-volume mountPath: /etc/pki/tls/openssl.cnf subPath: openssl.cnf - name: utimaco-cfg-volume mountPath: /etc/utimaco/cs_pkcs11_R3.cfg subPath: cs_pkcs11_R3.cfg - name: cert-volume mountPath: /certs restartPolicy: Never backoffLimit: 4
Replace <docker_username> with your actual Docker Hub username for the images you built and pushed to your repository.
-
Apply the Job.
Apply Key Generation Job
-
Verify the Job completion.
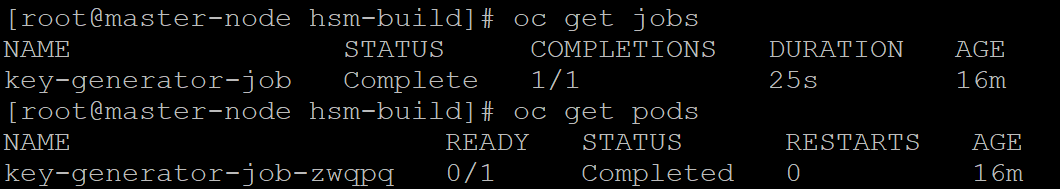
Verify Key Generation Job