1. Generate an EC keypair on Utimaco HSM.
|
›_ Console |
|---|
|
Provide information when prompted.
Here:
-
EC is the key algorithm
-
NONE is the keystore for HSM
-
PKCS11IMPLKS is the storetype
-
IBMPKCS11Impl-CryptoServer is the provider name
-
ibmec is the key name that will be generated on Utimaco HSM
Provide the keystore password when prompted.
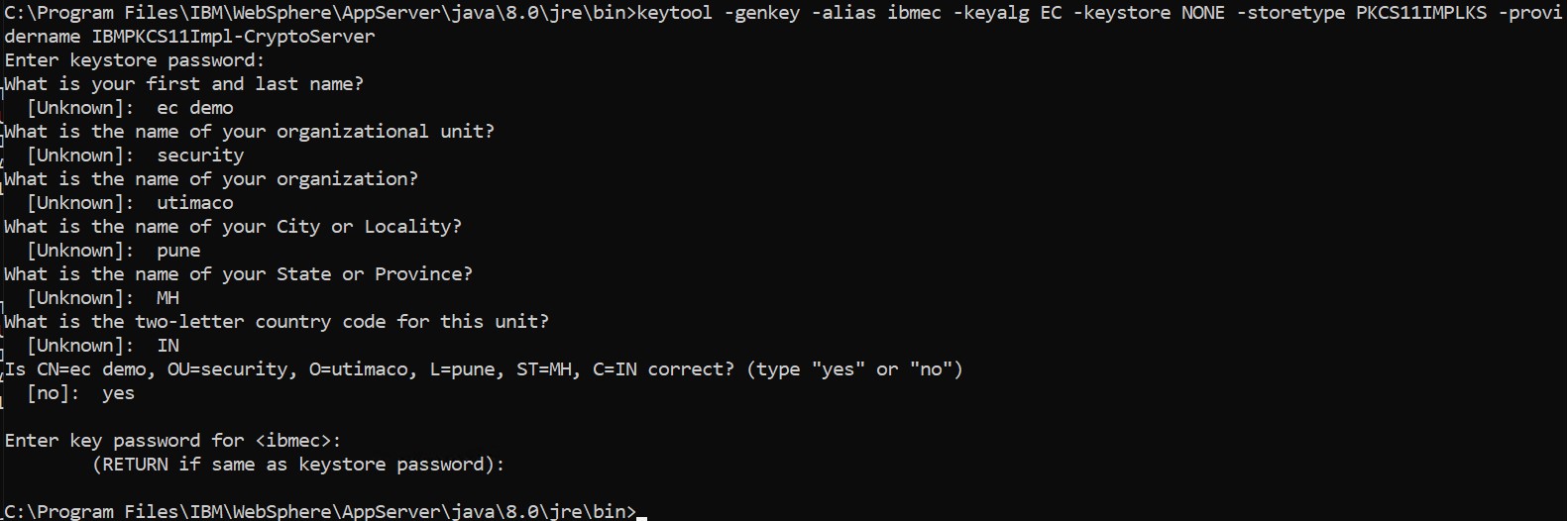
Key generation using keytool command
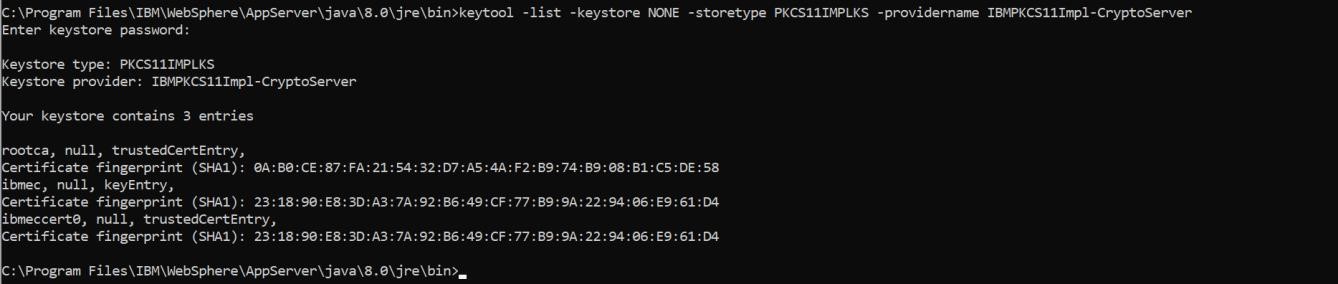
2. Verify the entry with same alias name is generated using keytool command.
|
›_ Console |
|---|
|
Here:
-
NONE is the keystore for HSM
-
PKCS11IMPLKS is the storetype
-
IBMPKCS11Impl-CryptoServer is the provider name
Provide the keystore password when prompted.
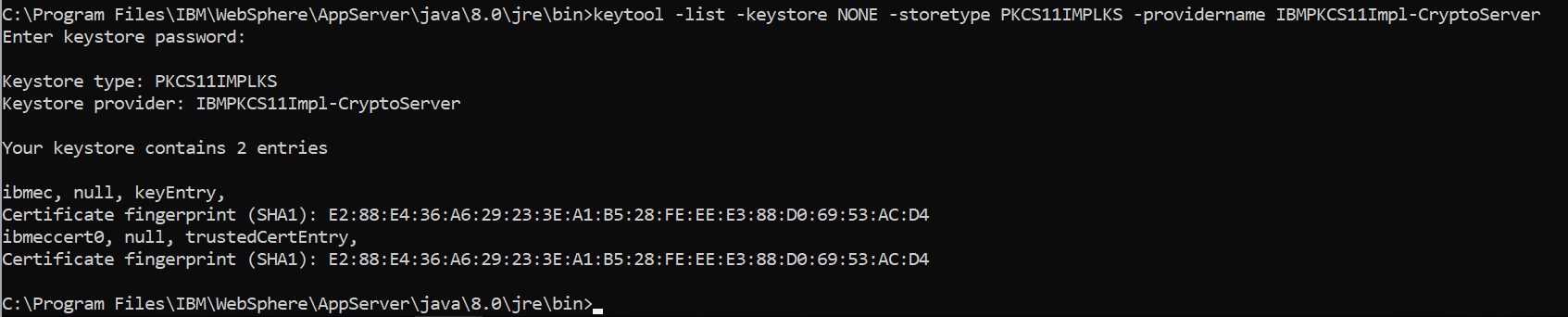
Keytool list command output
-
List the objects using p11tool2.
|
›_ Console |
|---|
|
Enter user PIN when prompted.
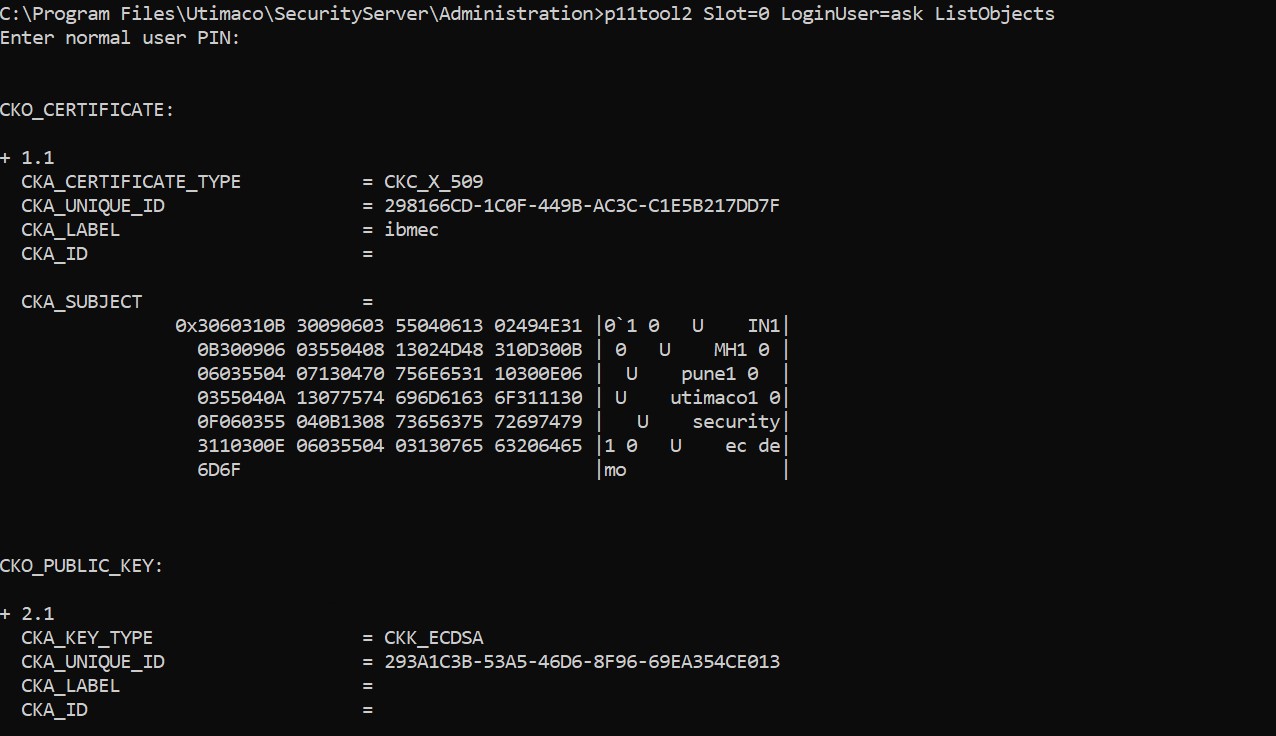
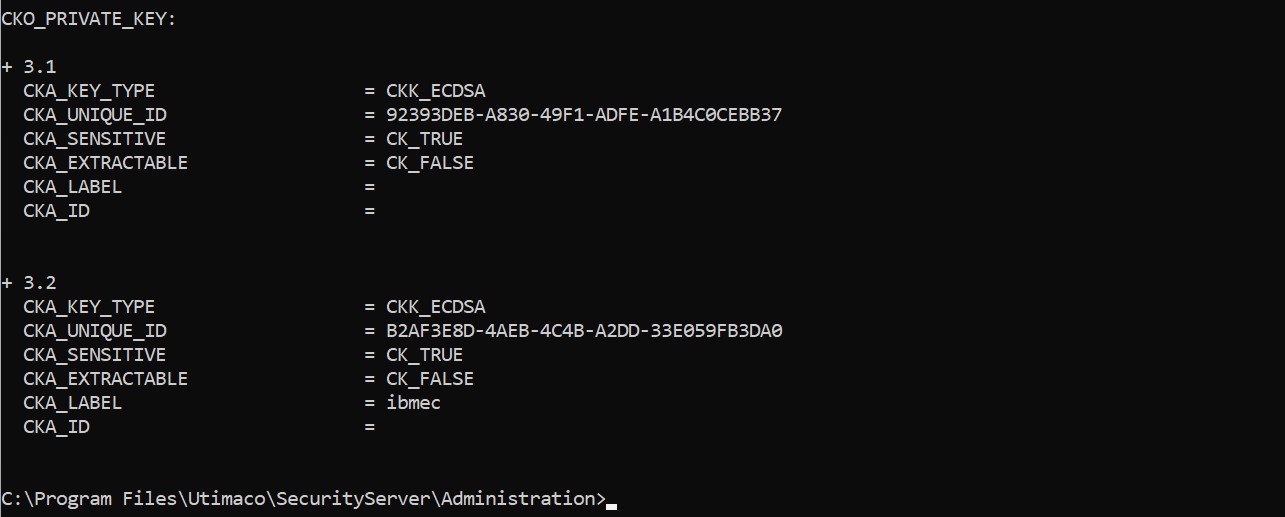
ListObjects output using p11tool2
4. Generate a CSR using Keytool command.
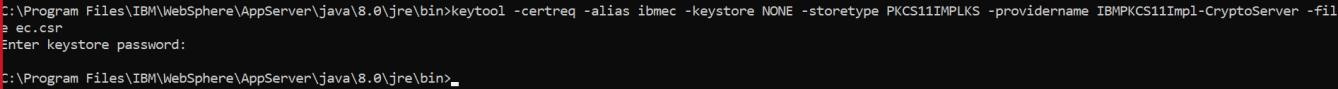
Generate CSR command output
Here:
-
NONE is the keystore for HSM
-
PKCS11IMPLKS is the storetype
-
Provide the keystore password when prompted
-
IBMPKCS11Impl-CryptoServer is the provider name
-
ibmec is the key name
-
ec.csr is the CSR file name that will be generated
Provide the keystore password when prompted.
-
Get this CSR signed by CA.
-
Copy the signed certificate and root CA certificate on the IBM WebSphere application server.
-
Import Root CA certificate into HSM keystore.
|
›_ Console |
|---|
|
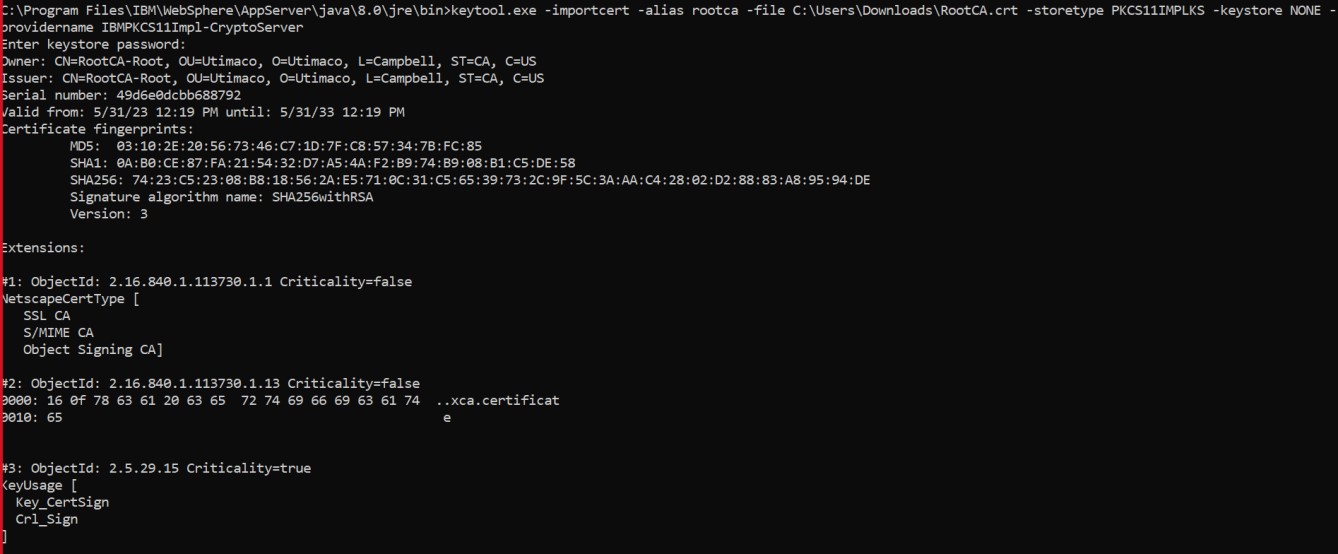
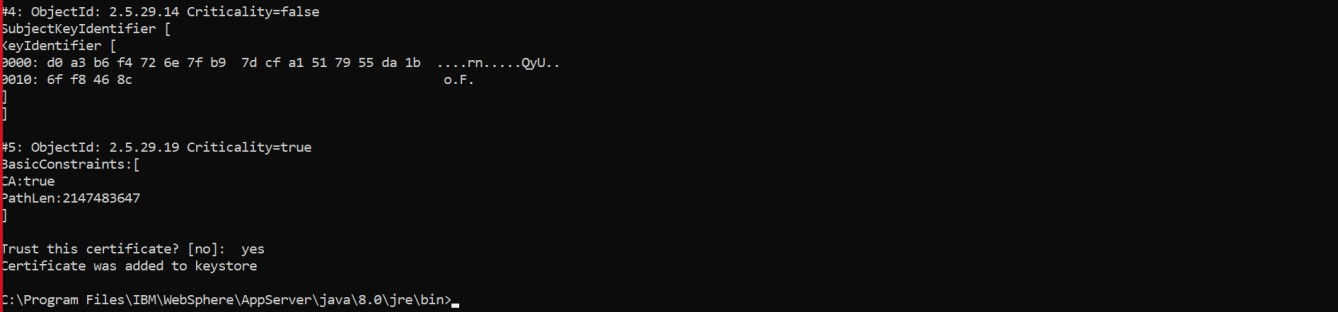
Importing root CA certificate into keystore
-
Import the signed certificate reply using the command below.
|
›_ Console |
|---|
|
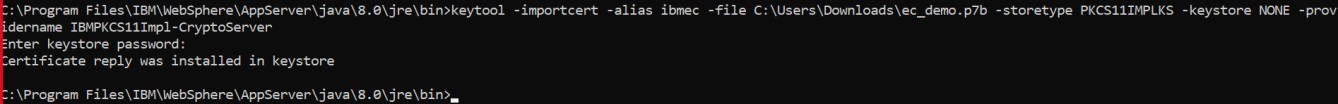
Importing user certificate into keystore
-
Verify that the keytool command shows the signed certificate as well as root CA certificate.
|
›_ Console |
|---|
|
Here:
-
NONE is the keystore for HSM
-
PKCS11IMPLKS is the storetype
-
IBMPKCS11Impl-CryptoServer is the provider’s name
Provide the keystore password when prompted.
Keytool list output showing signed certificate as well as root CA certificate