-
Make sure Elasticsearch and Kibana are up and the Elasticsearch dashboard is accessible.
-
Make sure
ca.crtandca.keyfiles (created during Elasticsearch configuration) are available in theC:\elasticsearch\config\certsfolder. -
Create an
instance.ymlfile in theC:\logstash\logstash-certsdirectory and update it with the following configuration:
instances:
- name: "server"
ip:
- "Logstash host IP"
dns:
- "<hostname>" # hostname of Logstash machine
- "localhost"
Replace <logstash_machine_ip> and <hostname> with the actual Logstash host IP and hostname of the Logstash server.
-
Open PowerShell as an administrator from
C:\elasticsearch\binand enter the following command to generate a Logstash TLS certificate signed by CA:
.\elasticsearch-certutil.bat cert --pem --in "C:\logstash\logstash-certs\instance.yml" --out "C:\logstash\logstash-certs\logstash-certs.zip" --ca-cert "C:\elasticsearch\config\certs\ca.crt" --ca-key "C:\elasticsearch\config\certs\ca.key"
-
Unzip
logstash-certs.ziptoC:\logstash\certs. -
Update the
logstash.conffile in theC:\logstash\configdirectory with the following configuration:
input {
tcp {
port => 6514
ssl_enabled => true
ssl_certificate => "C:/logstash/certs/server.crt"
ssl_key => "C:/logstash/certs/server.key"
ssl_client_authentication => none
mode => "server"
}
}
output {
elasticsearch {
hosts => ["https://<elasticsearch host IP>:9200"]
user => "<elasticsearch user>"
password => "<elasticsearch password>"
ssl_enabled => true
ssl_certificate_authorities => "C:/elasticsearch/config/certs/ca.crt"
index => "eskm-tls-%{+YYYY.MM.dd}"
}
stdout => { code => rubydebug}
}
Replace <elasticsearch host ip> with the configured Elasticsearch server,<elasticsearch_user> and <elasticseacrh_password> with the created superuser credentials
-
Open PowerShell as an administrator from
C:\logstash\binand enter the following command to start Logstash:
.\logstash.bat -f C:\logstash\config\logstash.conf
-
Wait until the log displays
Pipelines running, which indicates Logstash is fully operational.
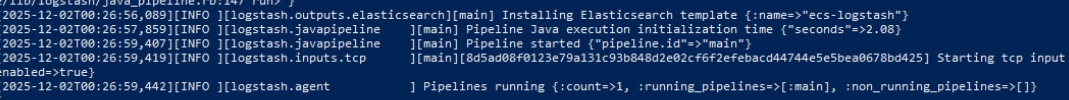
Logstash started
-
Open PowerShell as an administrator from
C:\logstash\certsand enter the following command to generate a client certificate:
openssl pkcs12 -export -in server.crt -inkey server.key -certfile "C:/elasticsearch/config/certs/ca.crt" -out eskm-syslog-client.p12
If you are using a different machine to access the ESKM Web UI, copy the CA certificate and the client certificate to that machine so they can be uploaded to ESKM.